February 29th, 2020 | 🕒
iSpeech.org ## # This module requires Metasploit: https://metasploit.com/download # Current source: https://github.com/rapid7/metasploit-framework ## class MetasploitModule < Msf::Exploit::Local Rank = ExcellentRanking
February 29th, 2020 | 🕒
iSpeech # Exploit Title: Aptina AR0130 960P 1.3MP Camera - Remote Configuration Disclosure # Author: Todor Donev # Date: 2020-02-23
February 29th, 2020 | 🕒
TTS # Exploit Title: Cacti 1.2.8 - Remote Code Execution # Date: 2020-02-03 # Exploit Author: Askar (@mohammadaskar2) # CVE:
February 29th, 2020 | 🕒
https://www.ispeech.org/text.to.speech # Title: Quick N Easy Web Server 3.3.8 - Denial of Service (PoC) # Date: 2019-12-25 # Author: Cody
February 29th, 2020 | 🕒
iSpeech Today digital transformation is a well-known concept. The growing connectivity of people, machines and even businesses has changed the
February 29th, 2020 | 🕒
iSpeech # Exploit Title: DotNetNuke 9.5 - File Upload Restrictions Bypass # Date: 2020-02-23 # Exploit Author: Sajjad Pourali #
February 29th, 2020 | 🕒
iSpeech In a recent Oxford Economics study, "Healthcare Gets Personal," 120 healthcare professionals were asked to respond to questions regarding
February 29th, 2020 | 🕒
Text to Voice # Title: ESCAM QD-900 WIFI HD Camera - Remote Configuration Disclosure # Author: Todor Donev # Date:
February 29th, 2020 | 🕒
iSpeech Data is at the very core of the business models of the future - and this means wrenching change
February 29th, 2020 | 🕒
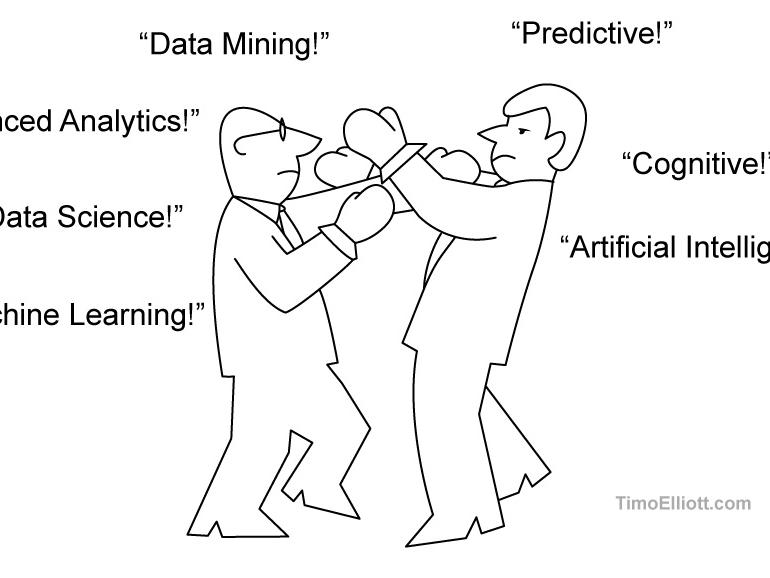
Text to Speech Voices Predictive analytics / machine learning / artificial intelligence is a hot topic - what's it about?
February 29th, 2020 | 🕒
Text to Speech # Title : AMSS++ v 4.31 - 'id' SQL Injection # Author : indoushka # Tested on:
February 29th, 2020 | 🕒
iSpeech.org In the last blog post, we discussed the CFO's role in digital transformatio and how CFOs can start applying












Gloss