March 13th, 2018 | 🕒
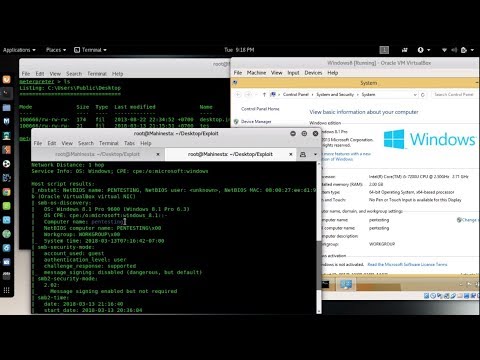
iSpeech.org Exploit MS17-010 vulnerability on windows 8.1/10/2016 using Metasploit + Unicorn | Bypass Antivirus | Unicorn | Kali Linux 2018
March 13th, 2018 | 🕒
https://www.ispeech.org This lesson explains the Principles of Security, under the course, "Cryptography and Network Security for GATE". The lesson explains
March 13th, 2018 | 🕒
iSpeech Hello everyone!! This is the 1st video of my new website hacking series, where I will teach how websites
March 13th, 2018 | 🕒
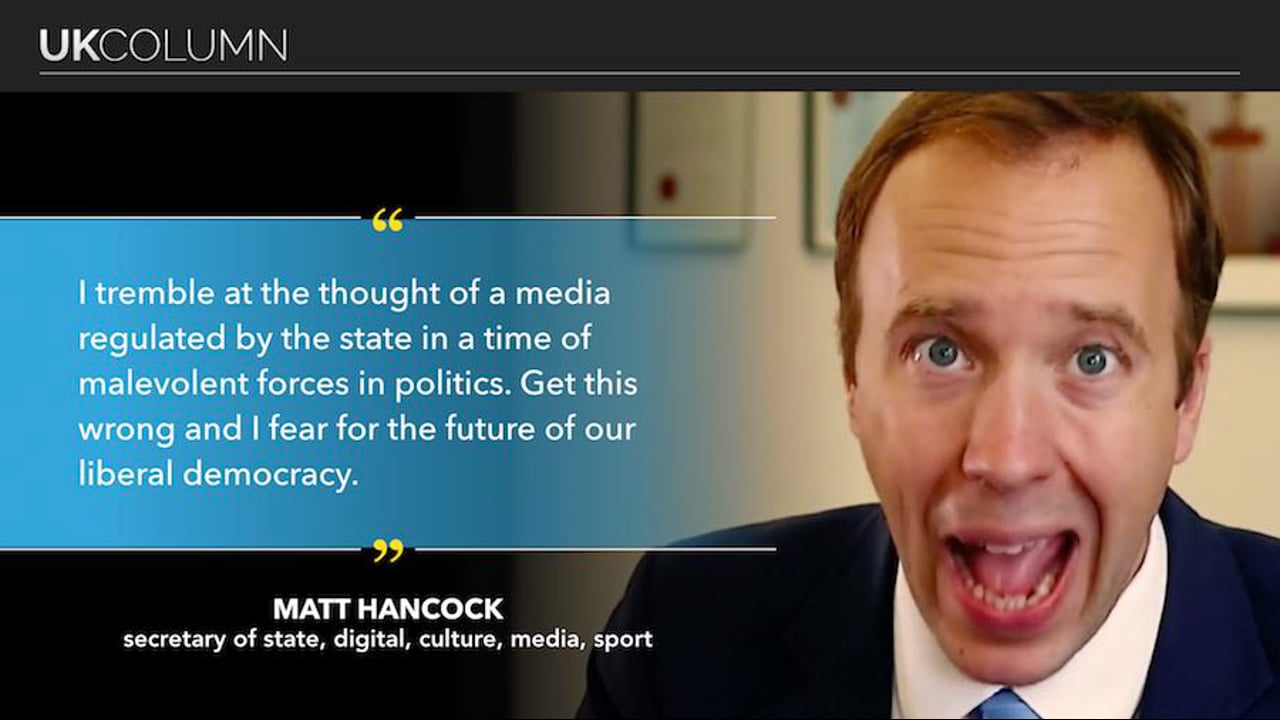
https://www.ispeech.org Brian Gerrish and Mike Robinson with today's news update from the UK Column. START – Poison used against Skripal:
March 13th, 2018 | 🕒
iSpeech The course you’re watching has been made available for free to YouTube due to poor quality audio. If you
March 13th, 2018 | 🕒
iSpeech.org Hello friends I am Shubham Kumar Sinha. Today In this video, we will be looking at the Fsociety hacking
March 13th, 2018 | 🕒
iSpeech Anthony Di Bello is Senior Director, Market Development, at OpenText. I knew him at Guidance Software before that, and
March 13th, 2018 | 🕒
Speech Synthesis Softcat's Chief Security Technologist, Adam Louca, looks at network segmentation as an effective technique for your cyber security.
March 13th, 2018 | 🕒
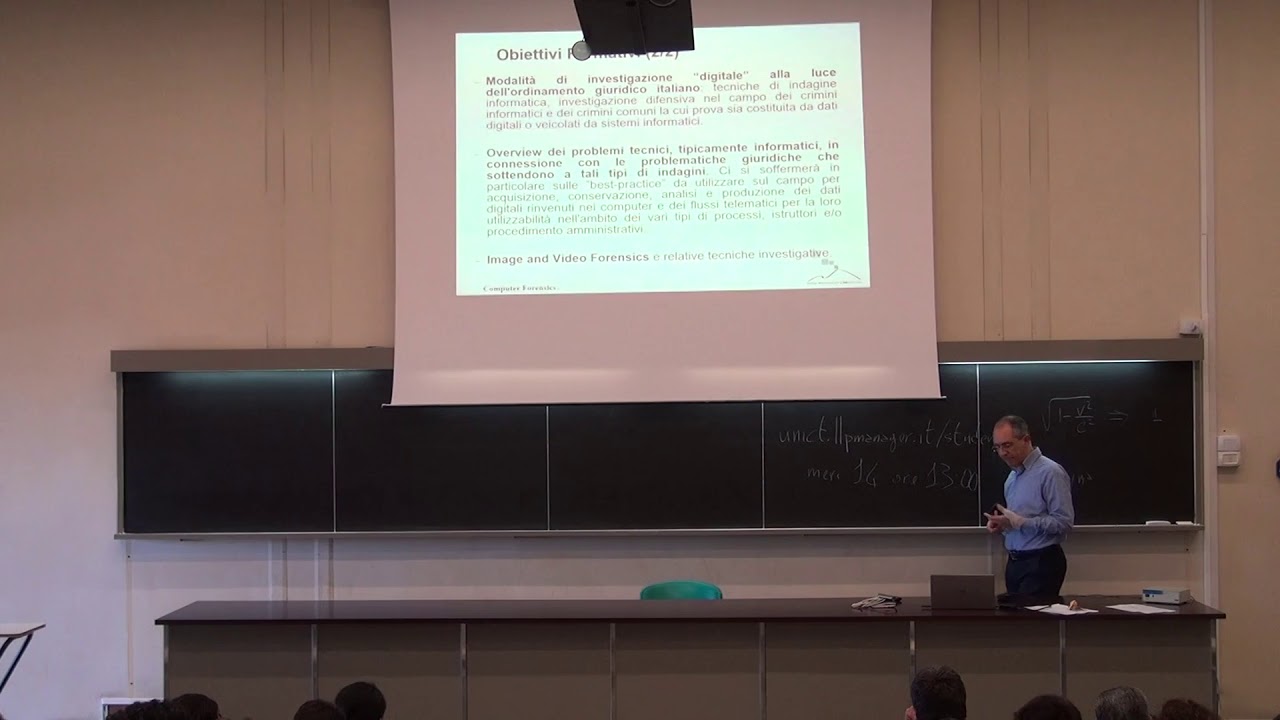
https://www.ispeech.org/text.to.speech Corso di Computer Forensics A.A. 2017-2018. Università degli Studi di Catania, Dipartimento di Matematica ed Informatica http://www.dmi.unict.it/~battiato/CF1718/CF1718.html 2018-03-13 10:08:27
March 13th, 2018 | 🕒
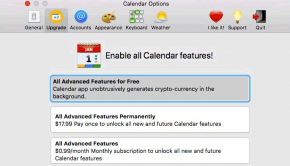
natural text to speech Nothing comes for free, especially online. Would you be okay with allowing a few paid services
March 13th, 2018 | 🕒
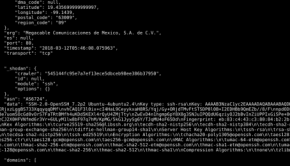
https://www.ispeech.orgMany-Eyes is a data collector that can be used for threat hunting and data collection, multi-threaded program to scrape data from multiple OSINT sources. This is cross
March 13th, 2018 | 🕒
Powered by iSpeechLast month, cybersecurity researchers demonstrated how to steal data from disconnected computers. Now they show how two computers
March 13th, 2018 | 🕒
iSpeech.orgA little VBScript that steal Wifi passwords from Windows Into the file WifiName.txt you can see the password of every saved wifi available on every windows computer



![fsociety Hacking Tools Pack - Mr. Robot Penetration Testing Framework [Hindi] ✔](https://www.torchsec.org/wp-content/uploads/2019/04/fsociety-Hacking-Tools-Pack-Mr.-Robot-Penetration-Testing-Framework-Hindi-✔-290x166.jpg)









Gloss