October 10th, 2017 | 🕒
https://www.ispeech.org/text.to.speech Want to join Lawline? Sign up here https://www.lawline.com/subscription Find out more about Developments in Data Breach Law: Seeking Redress
October 10th, 2017 | 🕒
https://www.ispeech.org Learn more at https://kirkpatrickprice.com/video/pci-requirement-6-1-establish-process-identify-security-vulnerabilities/ PCI Requirement 6.1 states, “Establish a process to identify security vulnerabilities, using reputable outside sources
October 10th, 2017 | 🕒
Text to Speech Voices Wim Mijs, Chief Executive Officer of the European Banking Federation, concludes the 2017 EBF Cybersecurity Summit
October 10th, 2017 | 🕒
iSpeech.org Anand Naik and Pankit Desai, Sequretek offers a comprehensive suite of products and services for securing information for their
October 10th, 2017 | 🕒
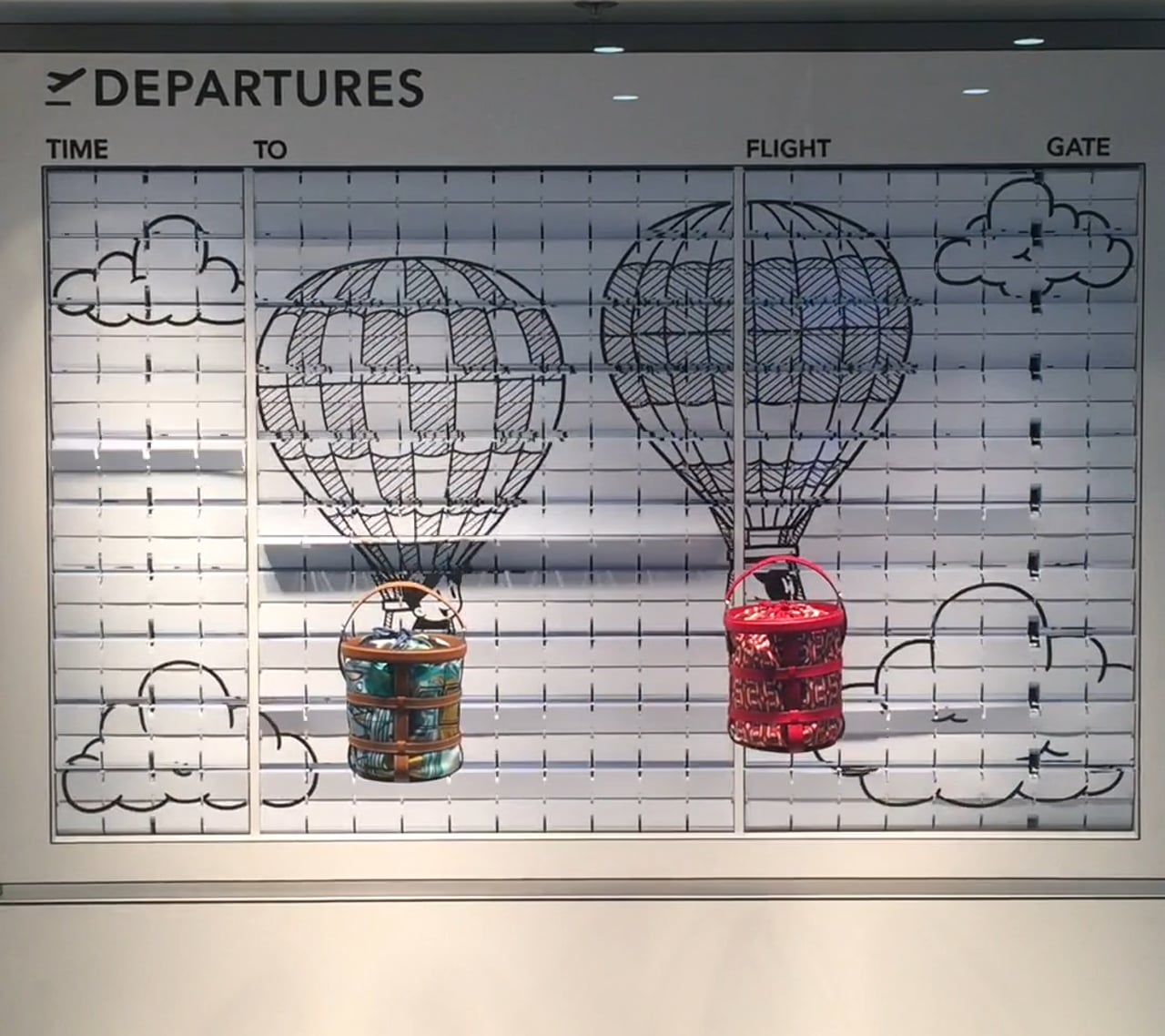
iSpeech.org Artist window for Hermès in Hong Kong International Airport. The concept of the window is initiated by "Object Sense".
October 10th, 2017 | 🕒
Convert Text to Speech how to configure SSH server in kali Linux. This tutorail is all about how to configure
October 10th, 2017 | 🕒
TTS Demo Metasploit Cheat Sheet Metasploit Cheat Sheet
October 10th, 2017 | 🕒
australian text to speech A penetration test is an effort to measure the security of an IT infrastructure by secure
October 10th, 2017 | 🕒
Convert Text to Speech Forrester Research announced today that Forrester.com experienced a security breach this week, attackers were ultimately detected
October 10th, 2017 | 🕒
iSpeechA slow data siphon for MySQL/MariaDB using bitwise operation on printable ASCII characters, via a blind-SQL injection Usage USAGE: blisqy.py
October 10th, 2017 | 🕒
https://www.ispeech.org NIELD (Network Interface Events Logging Daemon) is a tool to receive notifications from kernel through netlink socket, and generate


















Gloss