June 7th, 2017 | 🕒
iSpeech.org Basic Dynamic Malware Analysis with: VMware WorkStation = https://www.vmware.com/products/workstation Remnux = https://remnux.org/ ApateDNS = https://www.fireeye.com/services/freeware/mandiant-apatedns.html System Internal Suite (ProcMon,
June 7th, 2017 | 🕒
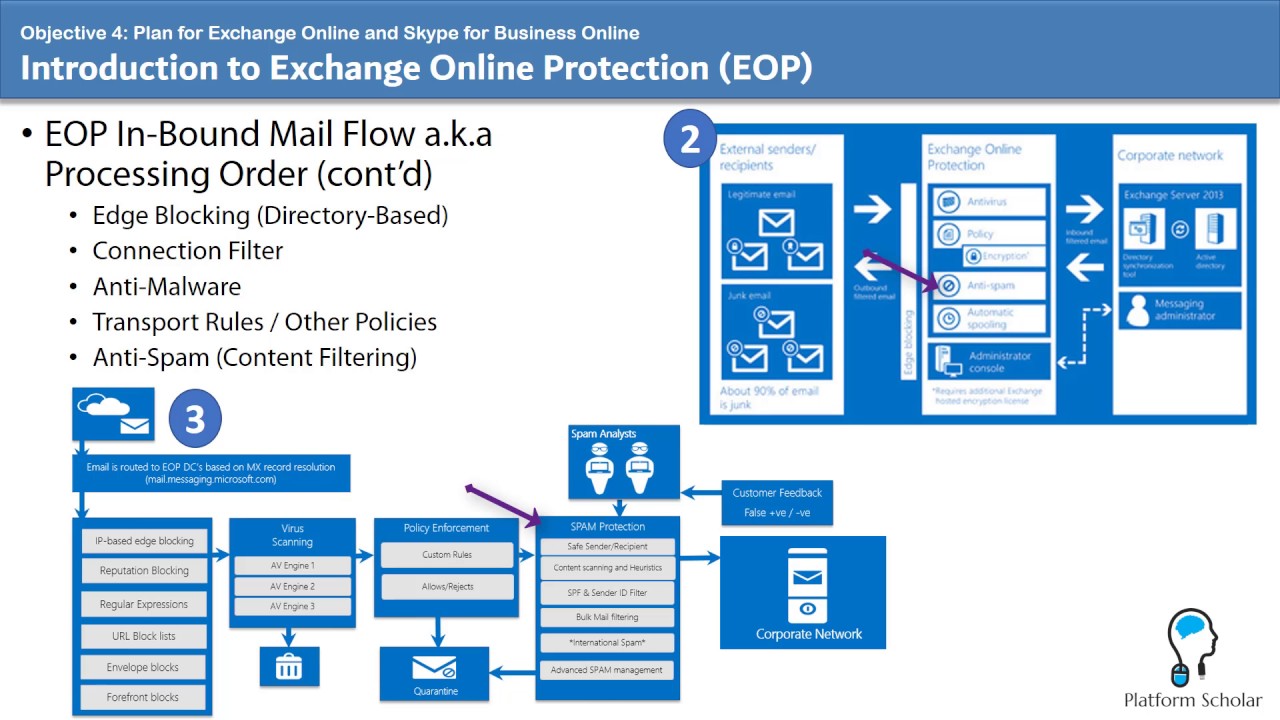
Powered by iSpeech MICROSOFT CHANGED THE FUNCTIONALITY OF THE ANTI-MALWARE FILTER FROM DELETE TO QUARANTINE ON THE DAY I RELEASED
June 7th, 2017 | 🕒
iSpeech.org FOR572: Advanced Network Forensics Analysis course author and instructor Phil Hagen introduces the SANS DFIR Network Forensics Analysis Poster,
June 7th, 2017 | 🕒
Powered by iSpeech Likes: 0 Viewed: source
June 7th, 2017 | 🕒
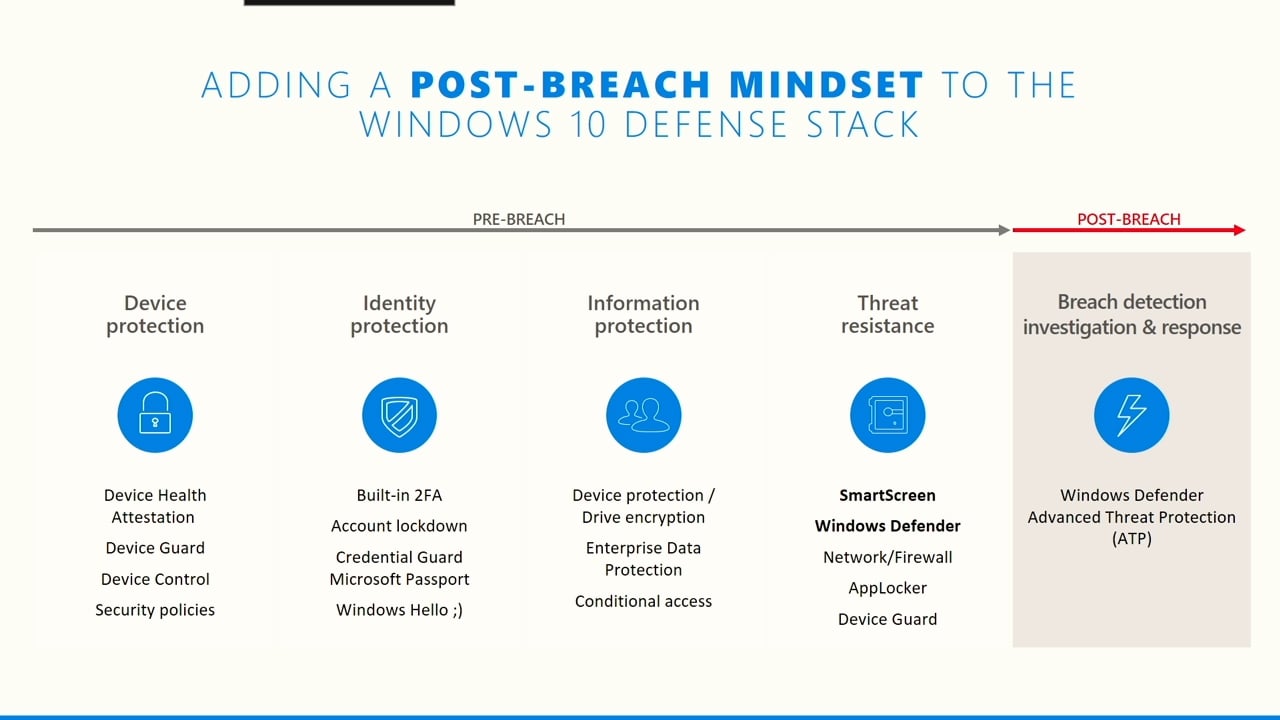
https://www.ispeech.org/text.to.speech Learn of the stages of cyber attacks including the Advanced Persistent Threat (APT) kill chain, WDATP detection capabilities including
June 7th, 2017 | 🕒
iSpeech This short animated video explains how Reed Smith’s Breach RespondeRS tool can help clarify your response to a data
June 7th, 2017 | 🕒
iSpeech.org Click focuses on cyber security, with a look at biometric identification and whether it really is keeping the nation's
June 7th, 2017 | 🕒
Text to Speech Title: Managing a Personal Data Breach Speaker: Atty. Ivy Grace Villasoto Policy Development Division Chief, National Privacy
June 7th, 2017 | 🕒
TTS Juniper Networks' security solution for hybrid and multi- cloud deployments, including AWS and Azure. video, sharing, camera phone, video













Gloss