April 20th, 2017 | 🕒
iSpeech.org Class Link: https://sumuri.com/course/windows-link-file-forensics/ Podcast: http://digitalforensicsurvivalpodcast.com/ Windows LINK files are a great source of information when your aim is proving
April 20th, 2017 | 🕒
iSpeech.org Viewers like you help make PBS (Thank you ?) . Support your local PBS Member Station here: https://to.pbs.org/donateinfi Only
April 20th, 2017 | 🕒
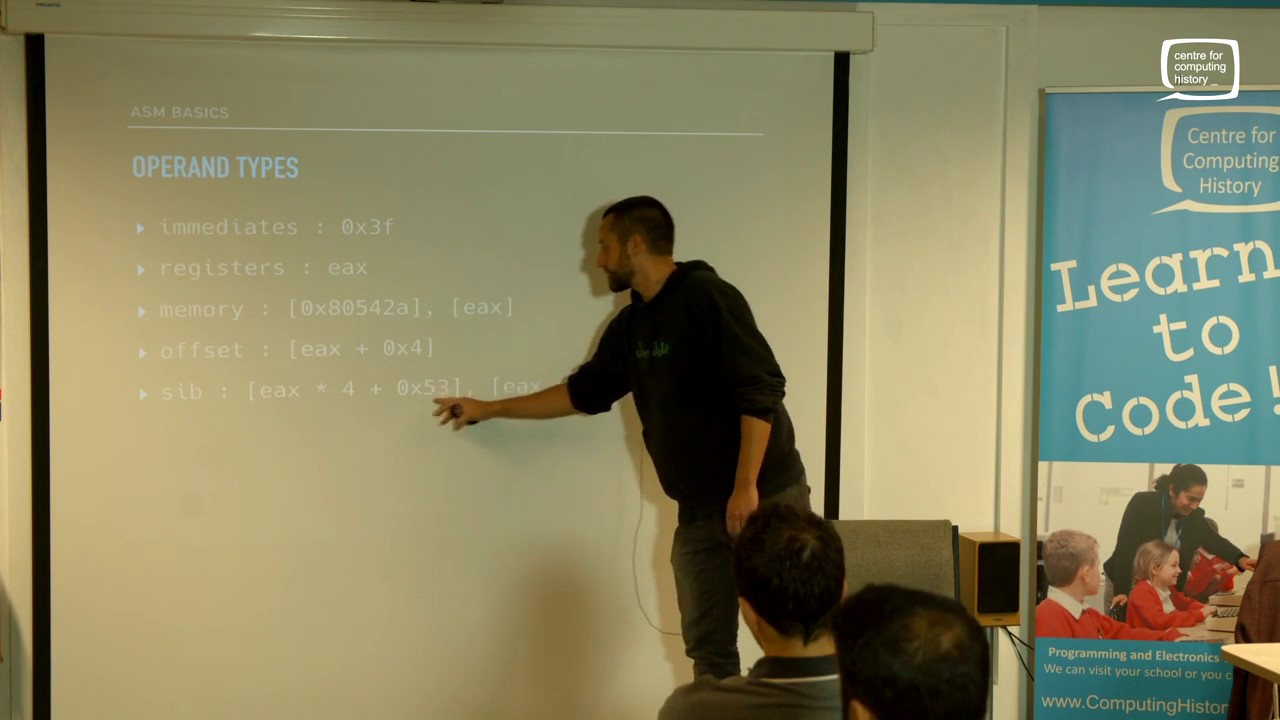
Text to Speech Filmed : 27-10-2016 A talk from the CamSec meeting at The Centre for Computing History about the
April 20th, 2017 | 🕒
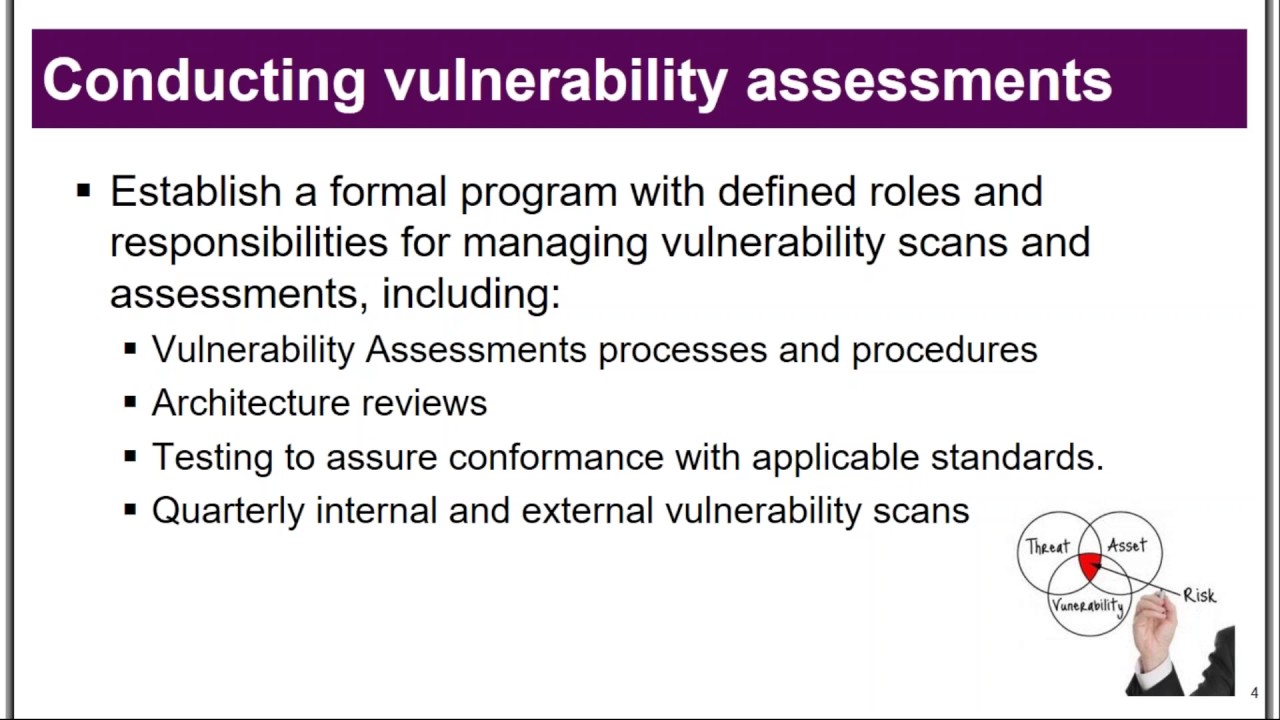
iSpeech.org The purpose of an organization’s Vulnerability Assessment program is to establish controls and processes that will help the organization
April 20th, 2017 | 🕒
iSpeech Many practices have concerns about increasing risk of HIPAA security audits, and whether internal security, training and documentation is
April 20th, 2017 | 🕒
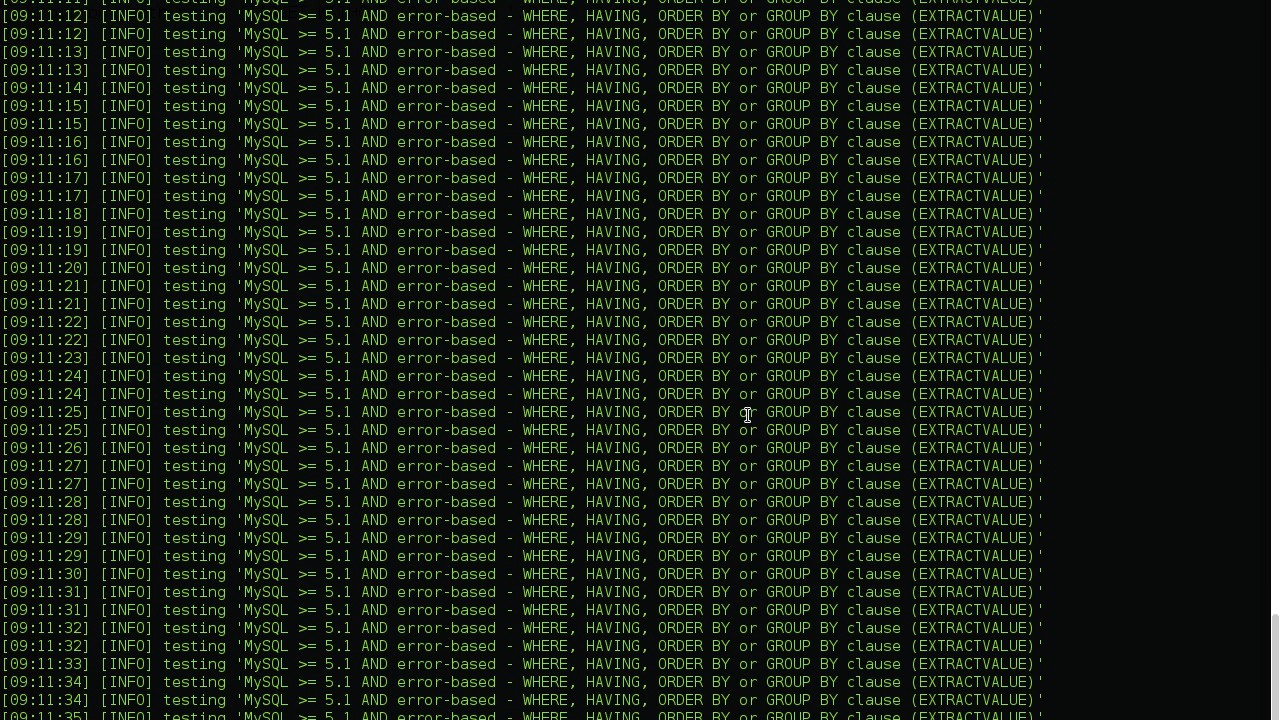
https://www.ispeech.org INSTALL : git clone https://github.com/r0oth3x49/Xpath.git && cd Xpath python xpath.py video, sharing, camera phone, video phone, free, upload 2017-04-20
April 20th, 2017 | 🕒
https://www.ispeech.org The video explains the RSA Algorithm (public key encryption) Concept and Example along with the steps to generate the
April 20th, 2017 | 🕒
iSpeech Types of digital signature approaches - RSA approach - DSS approach Digital Signature Algorithm with easy explanation.The Digital Signature
April 20th, 2017 | 🕒
Convert Text to Speech link website: https://www.exploit-db.com 2017-04-20 14:53:47 source
April 20th, 2017 | 🕒
https://www.ispeech.org Stored XSS on facebook.com Write-up : https://opnsec.com/2018/03/stored-xss-on-facebook/ Fixed! 2017-04-20 14:49:14 source
April 20th, 2017 | 🕒
iSpeech CrossSite Scripting - in short: XSS - is one of the most common weaknesses in software development. This applies
April 20th, 2017 | 🕒
iSpeech.org Cybersecurity has been a hot topic in the world of healthcare IT with the focus mostly on computer networks.
April 20th, 2017 | 🕒
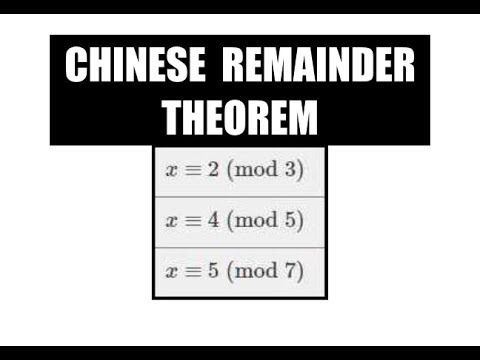
iSpeech Step by step instructions on how to use The Chinese Remainder Theorem to solve a system of linear congruence.
April 20th, 2017 | 🕒
Powered by iSpeech In this video, I explain the fundamentals concept of cryptography like types of crypt analysis, symmetric &














Gloss