December 28th, 2016 | 🕒
text to speech Download setup file: https://goo.gl/4XqSGu License file: https://goo.gl/UMiZRK Avast Internet Security 2018 With License Key file 2020 2016-12-28
December 28th, 2016 | 🕒
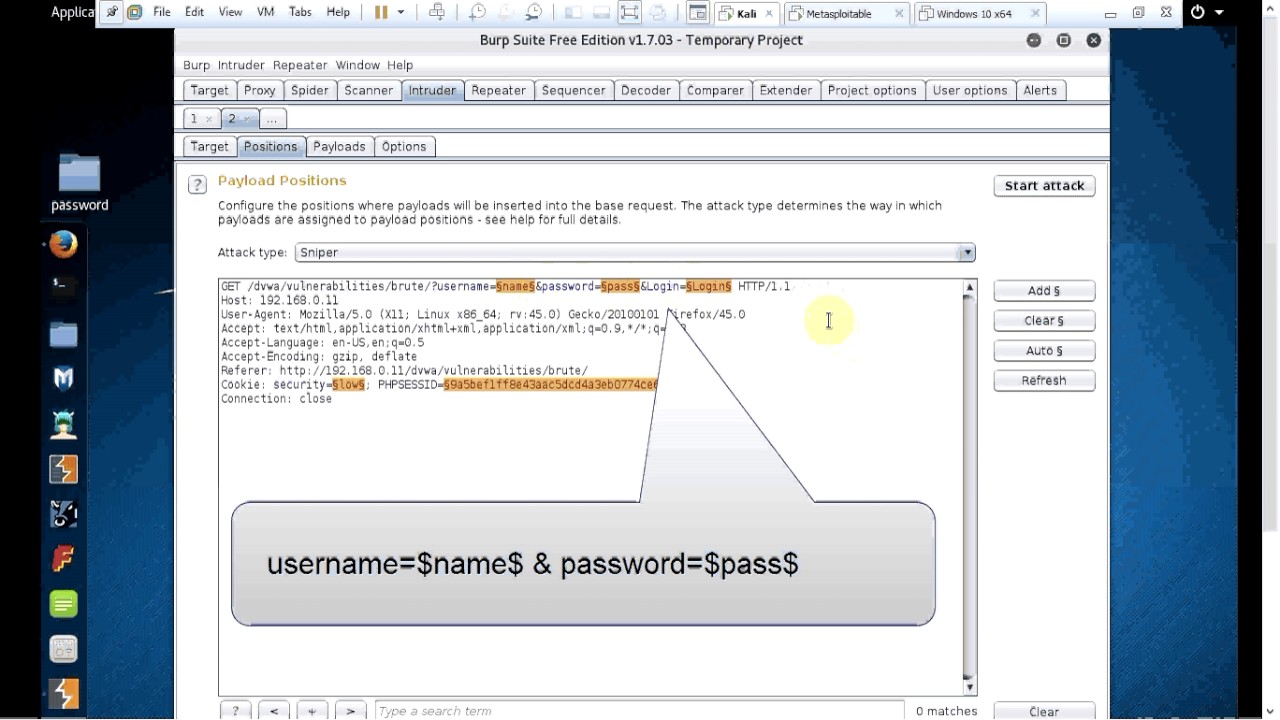
iSpeech This tutorial explains how to do an attack on web application to identify the user ID and password. I
December 28th, 2016 | 🕒
iSpeech ------------------------------------------------------------------------------------- الجزء الثاني من الفيديو.. ------------------------------------------------------------------------------------- الموقع المستخدم في الشرح (موقع التشفير) http://www.waraxe.us/sql-char-encoder.html ------------------------------------------------------------------------------------- -------------( الأوامر المستخدمـة.: )--------------------- group_concat(table_name)
December 28th, 2016 | 🕒
iSpeech In this demonstration I will show you how to add the F5 appliance into GNS3 pentesters virtual lab. This
December 28th, 2016 | 🕒
Powered by iSpeech In this demonstration I will show you how to add a CheckPoint appliance into GNS3 pentesters virtual
December 28th, 2016 | 🕒
Text to Speech Voices In this tutorial we will be exploring that how to make #WiFi jammer with #kalilinux. WiFi
December 28th, 2016 | 🕒
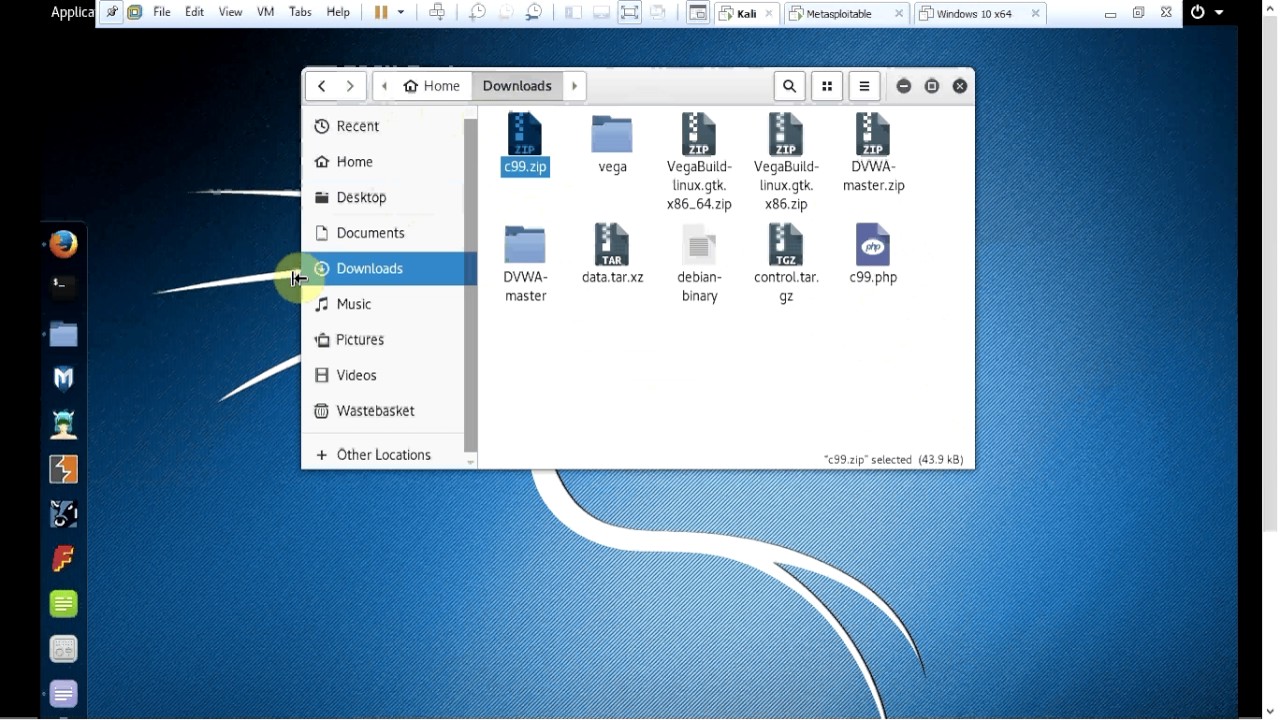
https://www.ispeech.org This tutorial will introduce you to the vulnerabilities could be exploited by uploading file (exploit) to the web server.
December 28th, 2016 | 🕒
https://www.ispeech.org This tutorial will explain how to do "cross-site forgery" attack. I have used DVWA to test the vulnerability and
December 28th, 2016 | 🕒
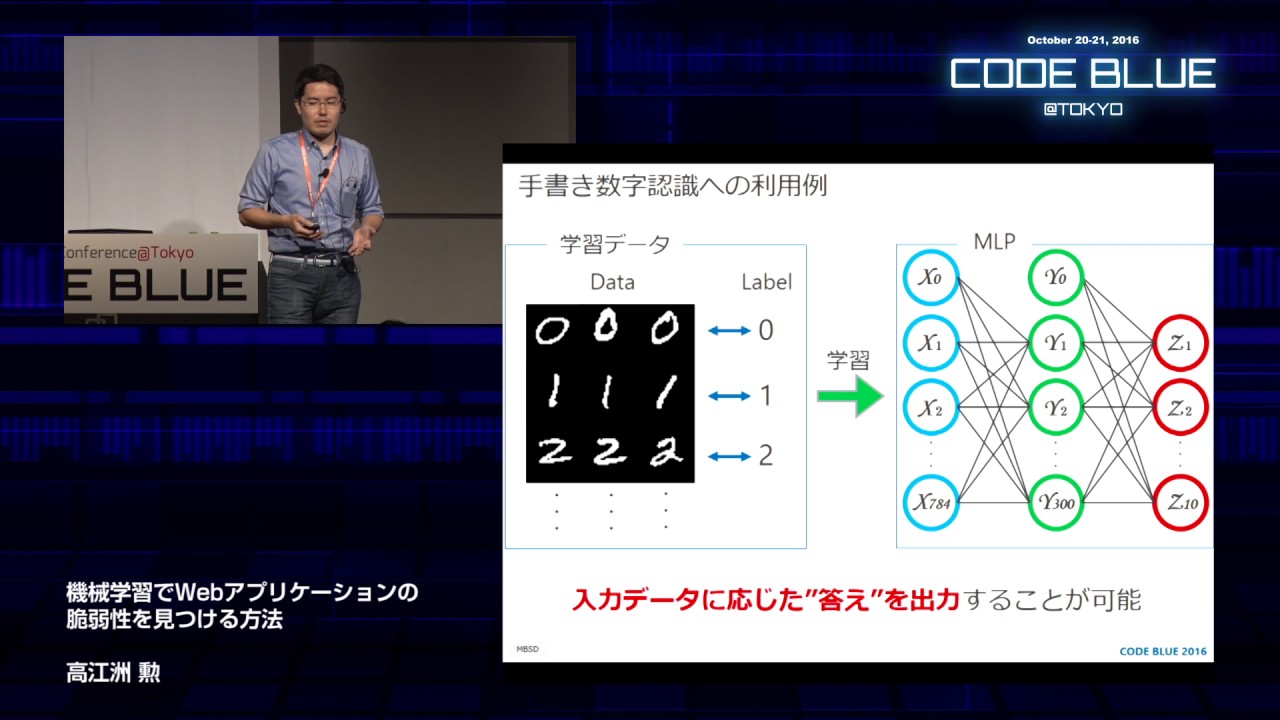
iSpeech.org In Japan, information security engineers are lacking. So, I am focused on artificial intelligence (AI) technology to solve the
December 28th, 2016 | 🕒
Powered by iSpeech This talk will show esoteric web application vulnerabilities in detail, these vulnerabilities would be missed in a
December 28th, 2016 | 🕒
Text to Speech AP CM Chandrababu Information About Cashless Transactions with Cyber Security 'TV5 News' is 'Telugu Live news' which
December 28th, 2016 | 🕒
Text to Voice BFSI Security Summit 2016 - Panel Discussion: Rise of Cyber Crime: Managing the Cyber Security Threats to
December 28th, 2016 | 🕒
Speech Synthesis A Multi-platform open source Binary Analysis and Reverse engineering Framework. The analysis of binary code is a crucial activity
December 28th, 2016 | 🕒
https://www.ispeech.org This vid explains how to uninstall Norton Security (NS) manually. Plz use this app uninstaller PRO@ https://macpaw.audw.net/c/376211/154407/1733 if you















Gloss