
Daily Archives: August 7, 2016
computer forensics degrees, online computer forensics courses
August 7th, 2016 | 🕒
french text to speech computer forensics degrees online computer forensics courses computer forensics classes online forensic psychology courses online computer
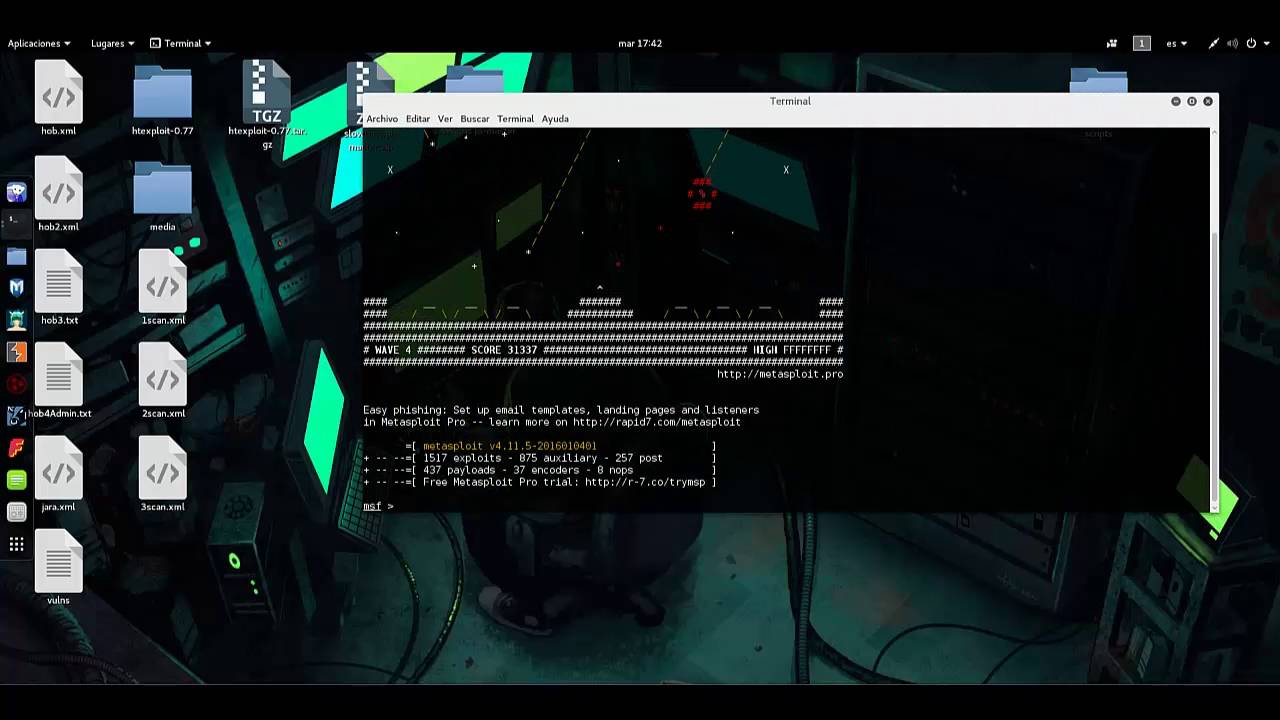
Pentesting con Kali Linux. Metasploit VM.
August 7th, 2016 | 🕒
https://www.ispeech.org web : hardsoftsecurity.es twitter: @DavidDeMaya Herramienta utilizada: Nmap Metasploit Metasploit VM Enlace al blog: Pentesting con Kali Linux. Metasploit
DARPA's Cyber Grand Challenge: Expanded Highlights from the Final Event
August 7th, 2016 | 🕒
https://www.ispeech.org/text.to.speech On August 4, 2016, seven high-performance computers successfully played a game of Capture the Flag during the Final Event
Sql Injection
August 7th, 2016 | 🕒
text to speech in this video i Explained about Sql injection and How to Prevent Sqlinjection Attacks in ASP.net 2016-08-07
Blind SQL Injection – Boolean based
August 7th, 2016 | 🕒
iSpeech.org In this tutorial i'll show you how to exploit a Blind SQL Injection. In this tutorial you will see
Omega-4
August 7th, 2016 | 🕒
iSpeech A young guy who works at a tech-firm goes about his daily routine, but the advent of a cyber-attack
A2SV – Auto Scanning to SSL Vulnerability
August 7th, 2016 | 🕒
Text to Speech1. A2SV? Auto Scanning to SSL Vulnerability. HeartBleed, CCS Injection, SSLv3 POODLE, FREAK... etc A. Support Vulnerability CVE-2014-0160]
DefCon: How the Hacker Tracker Mobile App Stays Secure
August 7th, 2016 | 🕒
iSpeech.orgLAS VEGAS—The DefCon hacker conference here at the Bally's and Paris Hotels is a massive affair with many rooms, events
Telegram Hack – Possible Nation State Attack By Iran
August 7th, 2016 | 🕒
iSpeech.orgSo there’s been a lot of news lately about the Telegram hack and how 15 million accounts were compromised, which















Gloss