June 20th, 2016 | 🕒
iSpeech.org Full DVD Version: http://www.russiancombat.com/spetsnaz-vs-boxing-how-to-fight-and-beat-a-boxer-dvd TRAINING: http://www.SystemaSpetsnaz.com SPETSNAZ DVDS: http://www.RussianCombat.com ****** SYSTEMA SPETSNAZ DVD #20: SPETSNAZ VS BOXING: HOW TO
June 20th, 2016 | 🕒
uk text to speech Do you know how much your business is at risk? Do you know how cyber attacks
June 20th, 2016 | 🕒
Powered by iSpeech 2016-06-20 16:16:51 source
June 20th, 2016 | 🕒
https://www.ispeech.org/text.to.speech All the highlights from our breakout session on combating emerging cyber threats during our Cybersecurity Summit. Moderated by Dave
June 20th, 2016 | 🕒
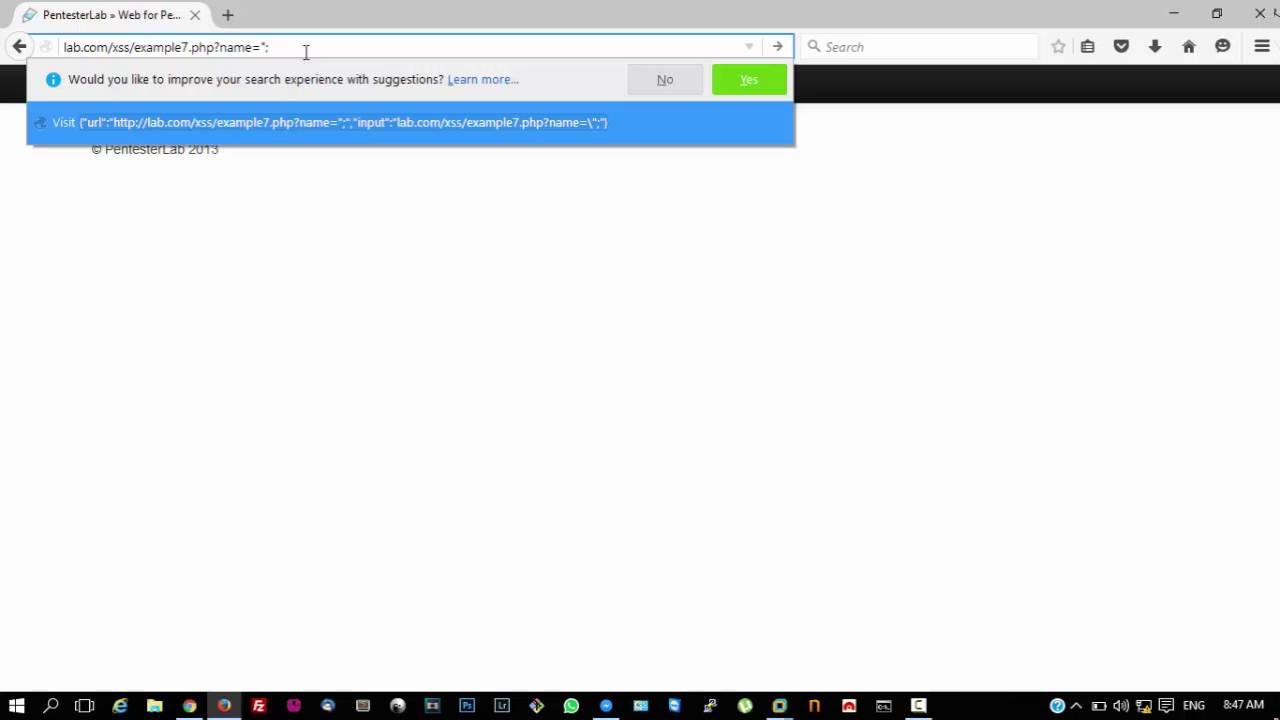
iSpeech.org Disclaimer: All information contained in this site and all software provided by it are intended solely for the purpose
June 20th, 2016 | 🕒
TTS This video demonstrates common Injection (A1) and Broken Authentication & Session Management (A2) flaws within a Grails application and
June 20th, 2016 | 🕒
iSpeech.org How Instagram is used in Osint Application. 2016-06-20 11:38:39 source
June 20th, 2016 | 🕒
TTSRecently Researchers mentioned that we can use the very recognized Telecom Flaw, to hack WhatsApp, Telegram, and Facebook. If we
June 20th, 2016 | 🕒
Convert Text to Speech ShellTer is an iptables-based firewall. What sets it apart from the rest is that it has
June 20th, 2016 | 🕒
https://www.ispeech.org Web Security Dojo is a preconfigured which is a stand-alone training environment for Web Application Security. In other words,
June 20th, 2016 | 🕒
iSpeech.org Ccrypt is a command-line utility for encrypting and decrypting files as well as streams. It replaces the old Unix
June 20th, 2016 | 🕒
iSpeech.org PytheM is a python network/pentesting tool. Same has been developed in the hope that it will be useful and
June 20th, 2016 | 🕒
iSpeech.org Site:- SecurityTraning – Ethical Hacking Tutorials, Tips & Tricks Facebook Page: https://www.facebook.com/s3ctraining Twitter :- https://twitter.com/Inf0SecTraining 2016-06-20 03:55:26 source



















Gloss