January 30th, 2016 | 🕒
https://www.ispeech.org/text.to.speech America's Biggest Police Union 2.5 GB Database Leaked Online. An unknown hacker online breached the US biggest police union,(Fraternal
January 30th, 2016 | 🕒
Text to Voice IAN TRUMP OF LOGICNOW WONDERS WHETHER THE HUMBLE PING COULD BE OUR SAVIOUR This Government of Canada
January 30th, 2016 | 🕒
spanish text to speech voiceshping is a command-line oriented TCP/IP packet assembler/analyser. The interface is inspired to the ping unix
January 30th, 2016 | 🕒
iSpeechAccording to Dr.Web’s security researchers, Google’s official Play Store is extremely unreliable because over 60 Android games available on this
January 30th, 2016 | 🕒
TTSGoogle’s VirusTotal service has added a new tool that analyzes firmware, the low-level code that bridges a computer’s hardware and operating
January 30th, 2016 | 🕒
iSpeech.org This tool collects different artefacts on live Windows and records the results in csv files. With the analyses of
January 30th, 2016 | 🕒
Text to Speech Voices Cyber doing her first live stream 2016-01-29 23:33:23 source
January 29th, 2016 | 🕒
Powered by iSpeech Visual hacking is a term to describe information that is captured through unauthorized visual means. Beth Lowther
January 29th, 2016 | 🕒
https://www.ispeech.org/text.to.speech Work in Kali Linux 2017.1 Commands to install the Main Menu: apt-get update apt-get install alacarte Commands to install
January 29th, 2016 | 🕒
iSpeech.org thanks to mistejk for writing and sending this one in. very cool stuff! look at his submission/source code/site with
January 29th, 2016 | 🕒
iSpeech.org Se si utilizza un computer Windows per navigare su internet è molto probabile "cadere" in vere e proprie trappole
January 29th, 2016 | 🕒
iSpeech Recorded presentation from 4SICS conference on security in Industrial Control Systems, SCADA and critical infrastructure. Presenter Robert M. Lee
January 29th, 2016 | 🕒
Text to Speech With GFI LanGuard, you can perform multi-platform vulnerability scans such as Windows®, Mac OS®, Linux®; and iOS®,
January 29th, 2016 | 🕒
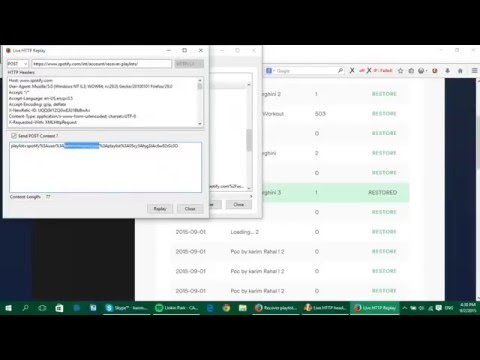
https://www.ispeech.org Bug Bounty Hacker - Spotify Bug Bounty 2016 - Privilege Escalation Vulnerability via CSRF URL: http://www.vulnerability-lab.com/get_content.php?id=1691 Article Guest: http://blog.detectify.com/2016/01/26/guest-blog-karim-rahal-on-a-spotify-playlist-hack/


















Gloss