December 30th, 2015 | 🕒
https://www.ispeech.org Governments post reports and data about their operations. Journalists publish documents from whistleblowers. But there is a third type
December 30th, 2015 | 🕒
https://www.ispeech.org/text.to.speech Governments post reports and data about their operations. Journalists publish documents from whistleblowers. But there is a third type
December 30th, 2015 | 🕒
iSpeech.org Introduction and gameplay for DefCon 1, Dos PC game produced by ROMulus Software in 1992 - http://www.squakenet.com/download/defcon-1/8664/ Defcon 1
December 30th, 2015 | 🕒
iSpeech.org FOCA (Fingerprinting Organizations with Collected Archives) es una herramienta creada por el hacker español Chema Alonso y su equipo,
December 30th, 2015 | 🕒
iSpeech http://robertsiciliano.com/ Security expert Robert Siciliano discusses ISIS Wants to Launch Cyberattack on the U S for @HotspotShield 2015-12-30 11:43:12
December 30th, 2015 | 🕒
https://www.ispeech.org/text.to.speech Elon knows when the Johnny Cab will arrive, North Korea is spying using Linux, Wireless charging is about to
December 30th, 2015 | 🕒
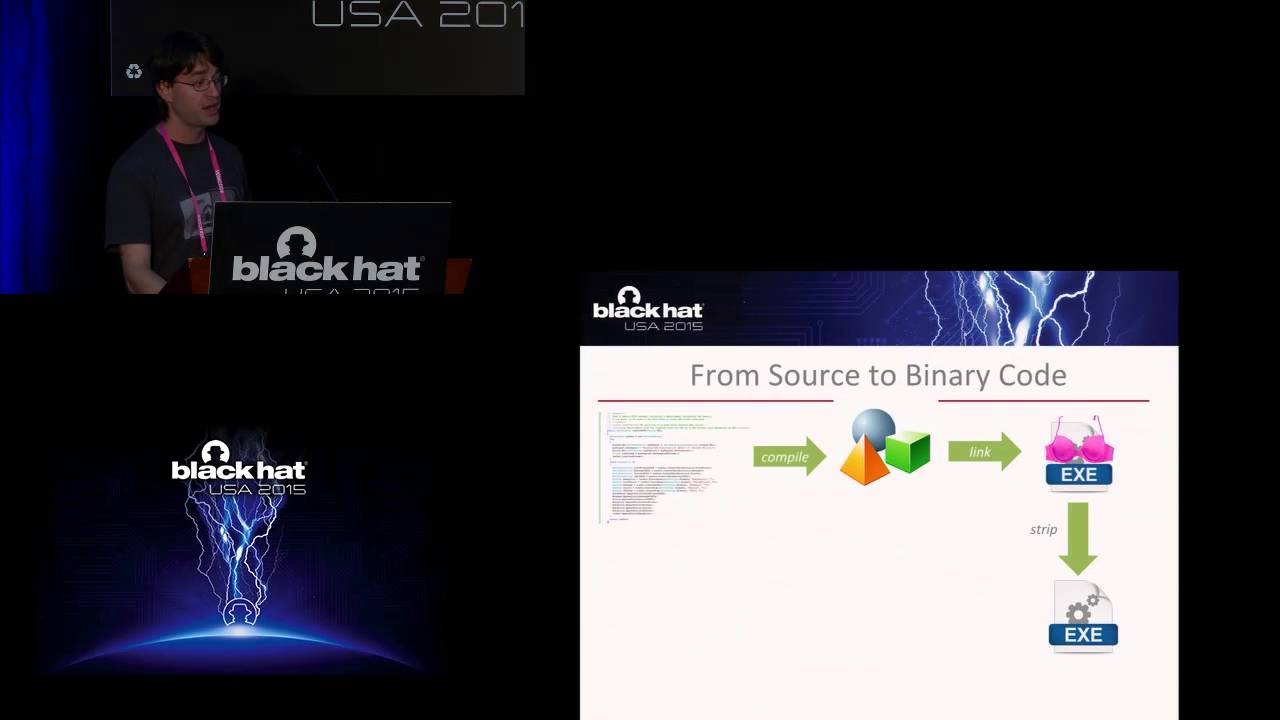
iSpeech.org by Christopher Kruegel & Yan Shoshitaishvili Over the last few years, as the world has moved closer to realizing
December 30th, 2015 | 🕒
iSpeech.org by Willis Vandevanter In this 25-minute briefing, we will discuss techniques for exploiting XXE vulnerabilities in File Parsing/Upload functionality.
December 30th, 2015 | 🕒
iSpeech Best antivirus 2016 for Windows 7/8/10 BitDefender ► https://goo.gl/QvzmUz MalwareBytes ► http://bit.ly/1OZUXWy Blog post: http://mytechmethods.com/guides/best-antivirus-2016 If you’re a Windows
December 30th, 2015 | 🕒
https://www.ispeech.org Security expert Robert Siciliano explains how vulnerable America may be to cyberattacks amid ISIS threats. video, sharing, camera phone,
December 30th, 2015 | 🕒
iSpeech Security analysts say breaches will be more frequent and damaging; Rich Edson provides insight on 'Special Report' Watch Doug
December 30th, 2015 | 🕒
https://www.ispeech.org PALO ALTO NETWORKS RESEARCHERS HAVE IDENTIFIED A UNIQUE MALWARE THAT INFECTS HOME PCS AND TRANSFORMS THEM INTO INTERNET PROXIES
December 30th, 2015 | 🕒
https://www.ispeech.orgRecently, security researchers at Symantec Corp identified a malware family that attacks Android devices located in China and blocks security
December 30th, 2015 | 🕒
iSpeech CenoCipher is a free, open-source, easy-to-use tool for exchanging secure encrypted communications over the internet. It uses strong cryptography



















Gloss