
Daily Archives: December 3, 2015
OSCP Review – Hack Naked News – #60
December 3rd, 2015 | 🕒
Powered by iSpeech Aaron reviews the Penetration Testing with Kali Linux course and OSCP test. Full Show Notes: http://wiki.securityweekly.com/wiki/index.php/Hack_Naked_TV_OSCP_Review →Visit
Exploiting HQL injection as blind SQL injection for Postgresql
December 3rd, 2015 | 🕒
iSpeech Exploiting HQL injection as blind SQL injection for Postgresql DBMS with sqlmap. 2015-12-03 17:11:19 source
Specimen Science: Ethics and Policy Implications, Panel 5: Ethical Challenges
December 3rd, 2015 | 🕒
iSpeech.org November 16, 2015 Many important advances in human health depend on the effective collection, storage, use, and sharing of
Finding XSS Vulnerabilities with Burp
December 3rd, 2015 | 🕒
Powered by iSpeech This is a tutorial on finding XSS vulnerabilities in a web application using one of OWASP's intentionally
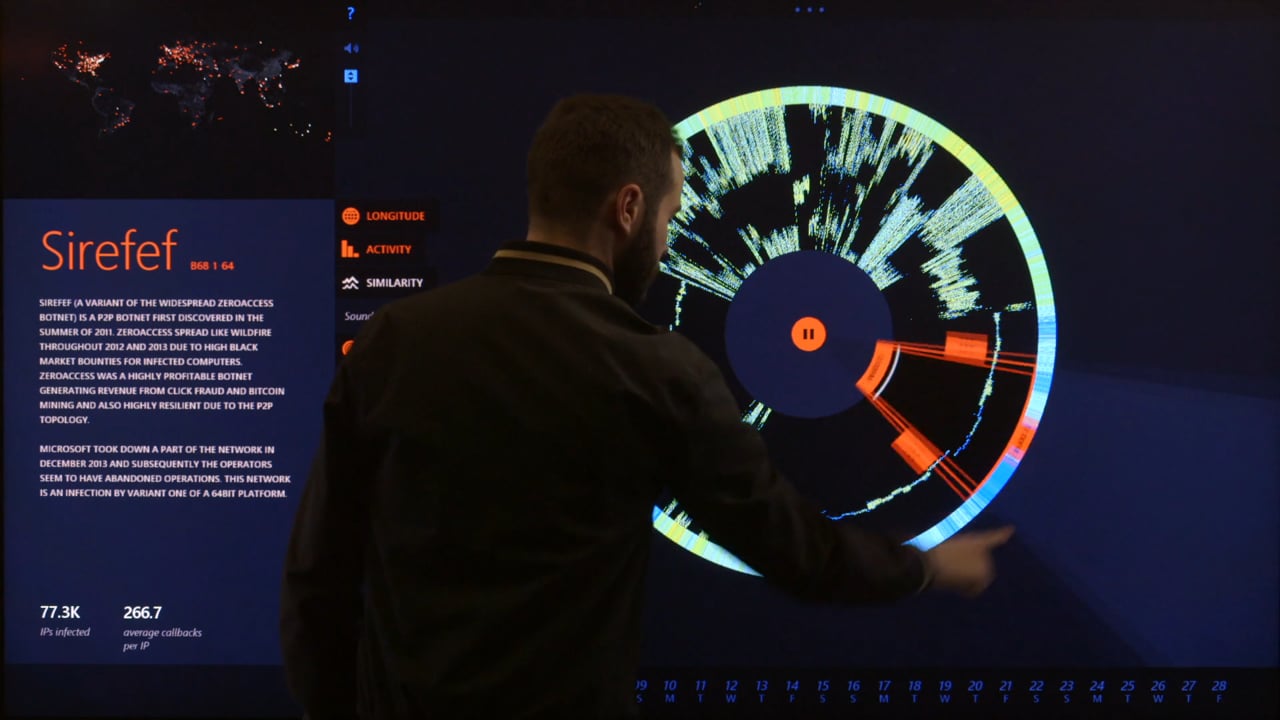
Botnet Activity in Real-Time
December 3rd, 2015 | 🕒
iSpeech The OCR began work on Specimen Box in 2014 at the request of Microsoft's Digital Crimes Unit. Microsoft's Cybercrime
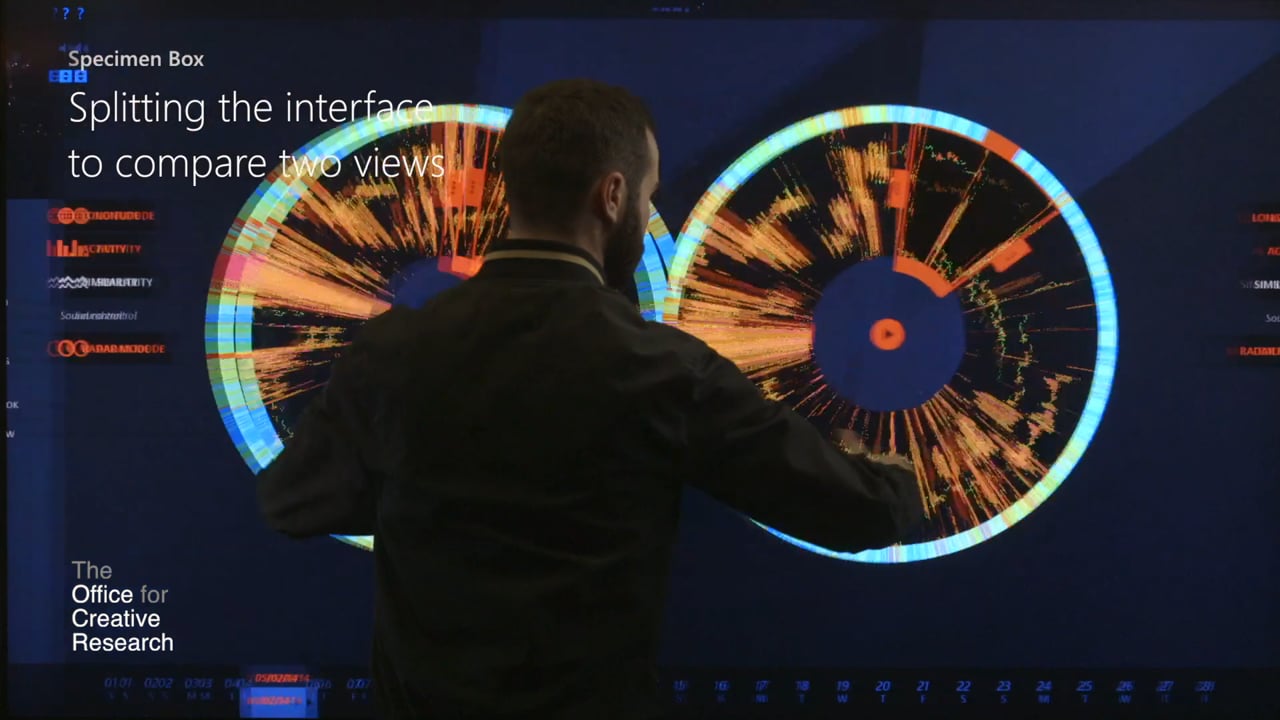
Cybercrime: Split and Compare
December 3rd, 2015 | 🕒
https://www.ispeech.org Split views allow two different data selections to be compared. The activity of one botnet strain can be compared
Specimen Box – Graph View
December 3rd, 2015 | 🕒
https://www.ispeech.org The OCR began work on Specimen Box in 2014 at the request of Microsoft's Digital Crimes Unit. Microsoft's Cybercrime
Cybercrime Data Sonification
December 3rd, 2015 | 🕒
https://www.ispeech.org Sonification allows users to probe the data for audible rhythms, cycles, and textures, calling attention to subtle time-based structures
Specimen Box – Deep Exploration
December 3rd, 2015 | 🕒
TTS Demo The OCR began work on Specimen Box in 2014 at the request of Microsoft's Digital Crimes Unit. Microsoft's
Keynote- What Got Us Here Wont Get Us There
December 3rd, 2015 | 🕒
iSpeech by Haroon Meer It's no secret that we have huge challenges in InfoSec: Every day we seem to pump
Cyber-Vulnerabilities in Aviation Today
December 3rd, 2015 | 🕒
iSpeech SEI Chief Operating Officer, Robert F. Behler presents Cyber-Vulnerabilities in Aviation Today. 2015-12-03 12:29:24 source
CYBER_WAR 1.0 – CHASING MY DIGITAL SELF | TRAILER
December 3rd, 2015 | 🕒
iSpeech.org We are in the middle of a worldwide cyber war that started in 2007, but nobody seems to worry
Creating and Fixing a SQL Injection Vulnerability
December 3rd, 2015 | 🕒
iSpeech A demonstration of how to create a SQL injection vulnerability in a WordPress application, how to exploit it and


















Gloss