August 5th, 2015 | 🕒
https://www.ispeech.org Cynthia Dwork, Microsoft Research Historical Papers in Cryptography Seminar Series http://simons.berkeley.edu/crypto2015/historical-papers-seminar-series/Cynthia-Dwork-2015-08-03 2015-08-05 17:47:56 source
August 5th, 2015 | 🕒
iSpeech Hello, I am In73ct0r d3vil and in Today's tutorial i will show you how to bypass Tough WAF using
August 5th, 2015 | 🕒
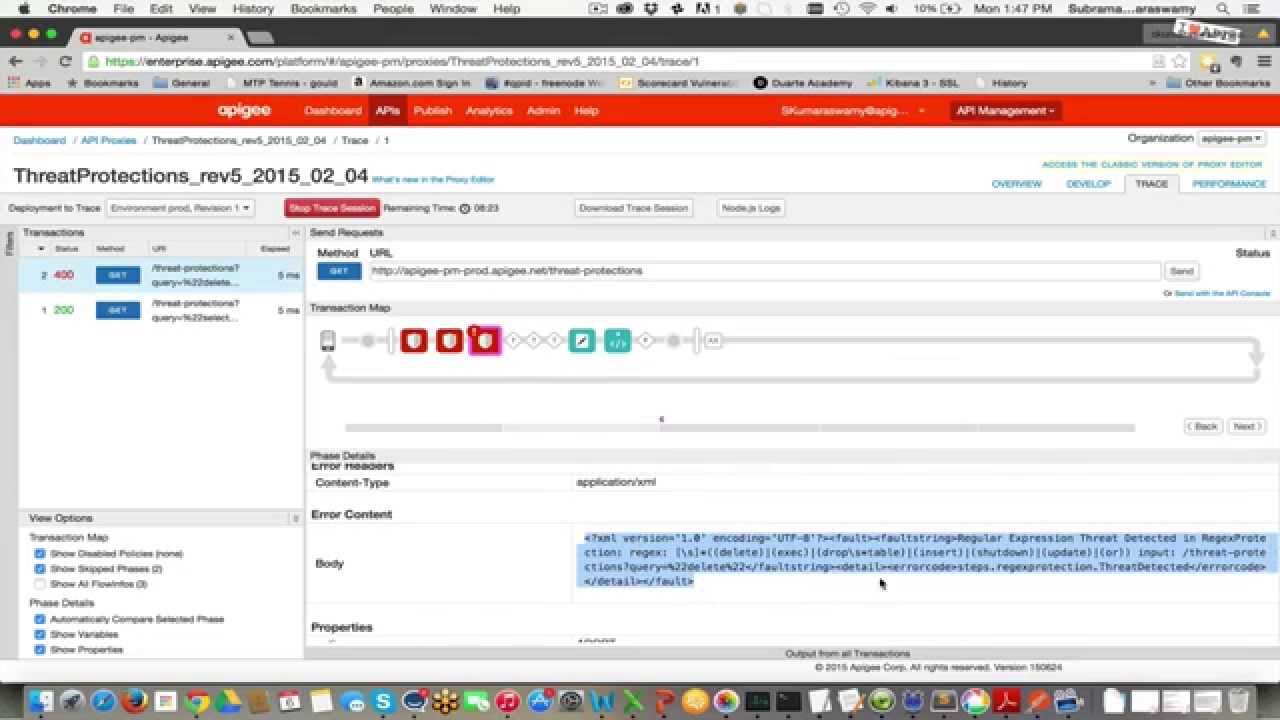
iSpeech OWASP identifies injection flaws, such as JSON, XML, SQL, as today’s most critical web application security threat. In this
August 5th, 2015 | 🕒
Text to Speech This is a short video that explains the general steps required for cyber criminals to weaponize a
August 5th, 2015 | 🕒
Free Text to Speech Sheila Fitzpatrick sheds light on the major differences between data privacy and data security in a
August 5th, 2015 | 🕒
iSpeech BlackArch Linux is an Arch Linux-based distribution for penetration testers and security researchers. The repository contains 1239 tools. You
August 5th, 2015 | 🕒
https://www.ispeech.orgFruityWifi is an open source wireless network auditing tool, it allows the user to deploy advanced attacks by directly using
August 5th, 2015 | 🕒
https://www.ispeech.org Yahoo's top websites fell victim to a “malvertising” attack within the company's ad network, although Yahoo will not reveal
August 5th, 2015 | 🕒
iSpeechA few days ago we wrote about the BIND software flaws that were discovered, affecting important companies, and last week















Gloss