August 1st, 2015 | 🕒
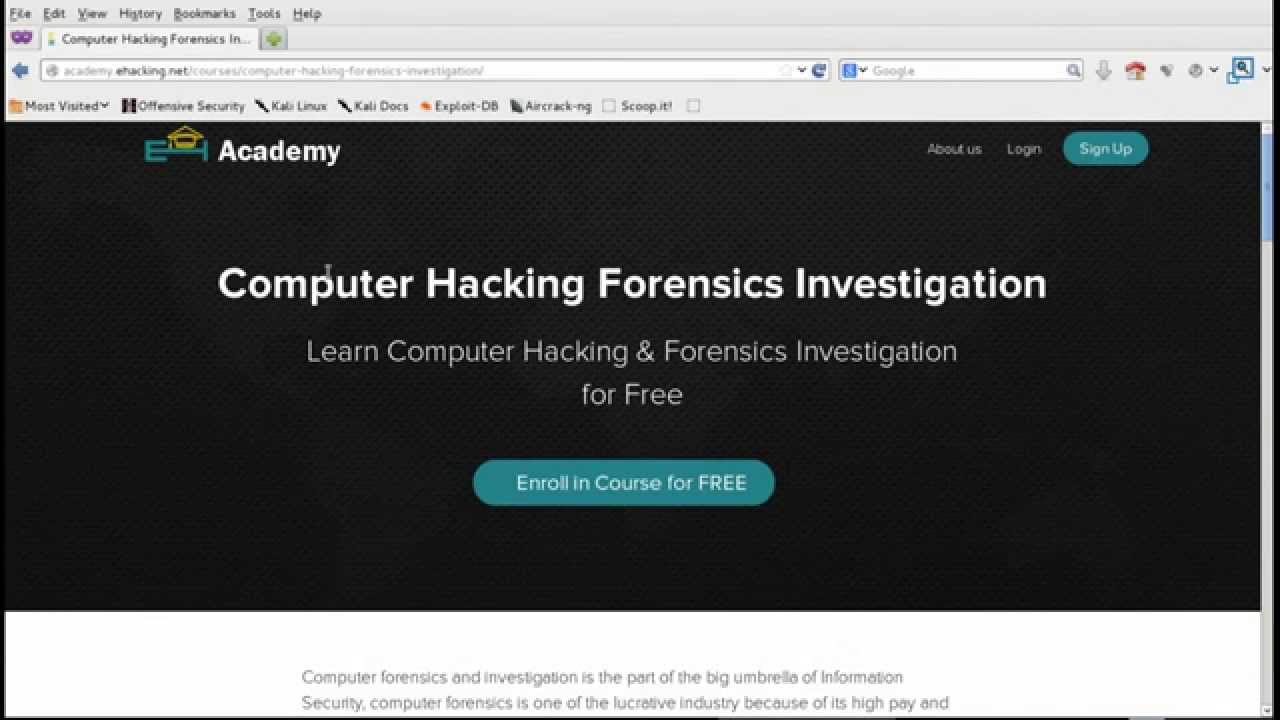
iSpeech.org EH Academy announces computer hacking forensics training course for FREE and for everyone. Enroll Now: http://academy.ehacking.net/courses/computer-hacking-forensics-investigation/ 2015-08-01 20:36:05 source
August 1st, 2015 | 🕒
TTS Demo Sql Injection Union based tutorial Union based string based error based double based WAF bypass 2015-08-01 17:19:48 source
August 1st, 2015 | 🕒
Powered by iSpeech Experts at Trend Micro discovered that cyber criminals are exploiting the popular Angler Exploit kit to find
August 1st, 2015 | 🕒
iSpeech This whole thing sounds like something straight out of CSI: Cyber with references to Drones, Tor, remailers, anonymous image
August 1st, 2015 | 🕒
iSpeech.org BitDefender hacked, unencrypted customer information compromised, hacker demands ransom from the AV firm in return for the exploit and
August 1st, 2015 | 🕒
https://www.ispeech.orgLooking at recent news stories points out that no organization is immune to being a target of a Distributed Denial
August 1st, 2015 | 🕒
iSpeech.org Researchers show how to remotely exploit the DRAM “Rowhammer” bug by using JavaScript Security researchers believe that the cyber
August 1st, 2015 | 🕒
german text to speechEver since its debut in the year 2013, Kali Linux users were waiting for a new and
August 1st, 2015 | 🕒
Text to Speech Voices Learning Linux for free gets no easier than this full Linux tutorial! Go from a beginner














Gloss