
Daily Archives: July 12, 2015
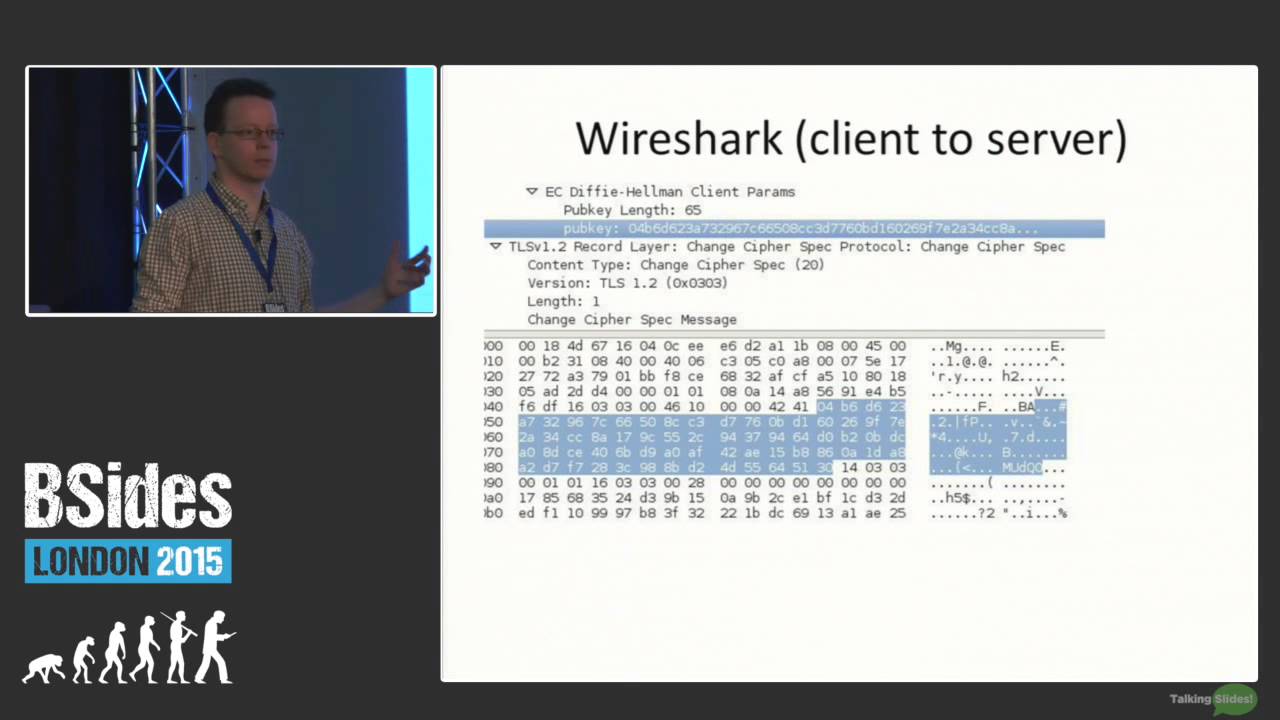
Martijn Grooten – Elliptic Curve Cryptography for those who are afraid of maths
July 12th, 2015 | 🕒
iSpeech Elliptic Curve Cryptography (ECC) is hot. Far better scalable than traditional encryption, more and more data and networks are
Cruel (SQL) Intentions – An Analysis of Malicious Intentions Behind Real World SQL Injection Attacks
July 12th, 2015 | 🕒
Powered by iSpeech Speaker: Ezra Caltum, Senior Security Researcher, Akamai's Cloud Security Intelligence "Technological Track: HackTalks Vs. TechTalks" Cyber Week
Cowrie SSH Honeypot
July 12th, 2015 | 🕒
Powered by iSpeech Cowrie is a medium interaction SSH honeypot designed to log brute force attacks and, most importantly, the
Hackers who targeted Facebook, Microsoft, Twitter and Apple, Pose Corporate Security Threat
July 12th, 2015 | 🕒
iSpeech.org Hacker group which targeted Facebook, Microsoft, Twitter and Apple is actively hacking to steal confidential information for profit A
UK to ban WhatsApp, iMessage and Snapchat Under New Laws
July 12th, 2015 | 🕒
Convert Text to Speech If you rely on messaging apps to remain in contact with your family members and friends,
Three UK politicians hacked while using open WiFi networks
July 12th, 2015 | 🕒
iSpeech.org A team of experts hacked three UK politicians while they were using unsecured WiFi networks to demonstrate the risks
Adobe to patch second Hacking Team Flash zero-day bug
July 12th, 2015 | 🕒
tts FireEye researcher unearths another Flash Player flaw in Italian firm's leaked docs Adobe next week will patch a second













Gloss