
Daily Archives: May 16, 2015
HackMiami Con – OSINT for the Enterprise: Taking Action with Public Threat Intelligence
May 16th, 2015 | 🕒
Powered by iSpeech SYNOPSIS: This presentation will cover numerous ways that enterprises are able to leverage threat intelligence in order
The Cryptography Behind Bitcoin
May 16th, 2015 | 🕒
iSpeech.org We recorded a presentation we gave to our class on the Cryptography Behind Bitcoin and shared it with you
Intro to Cryptography
May 16th, 2015 | 🕒
https://www.ispeech.org A brief overview of cryptography, and an introduction to a few beginner cryptographic systems, as well as how vulnerable
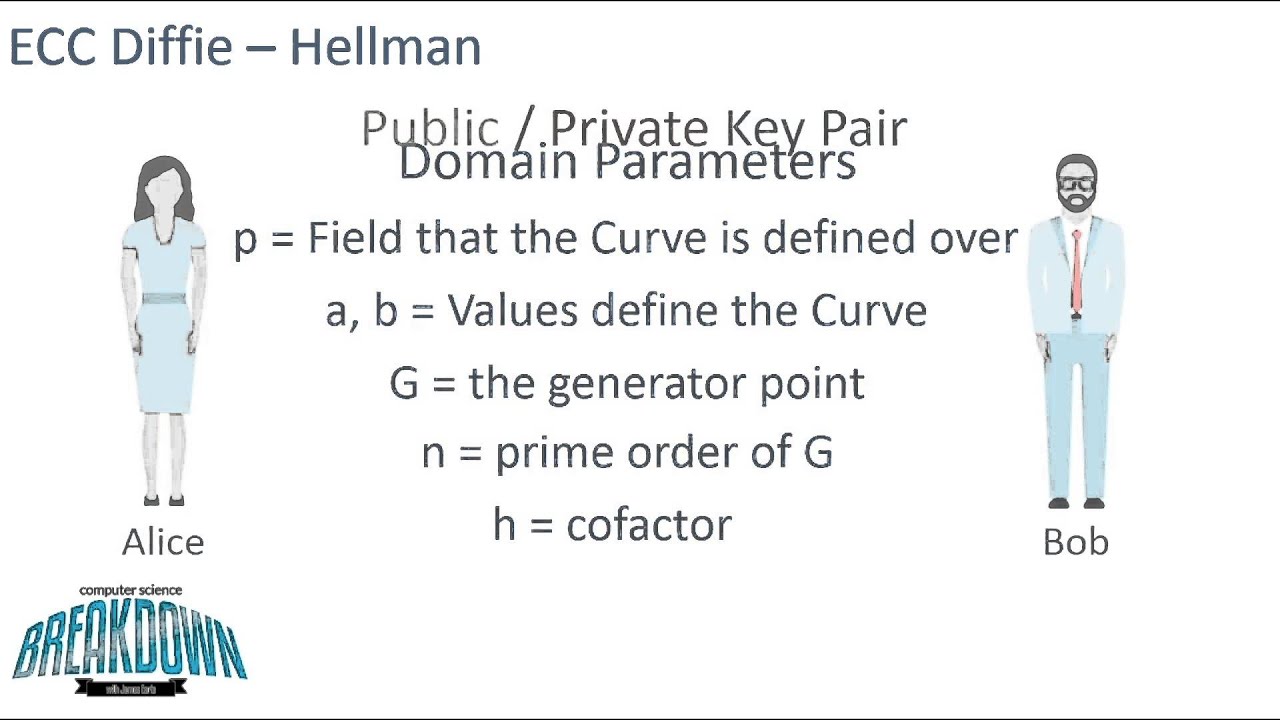
Elliptic Curve Cryptography & Diffie-Hellman
May 16th, 2015 | 🕒
iSpeech.org Today we're going over Elliptic Curve Cryptography, particularly as it pertains to the Diffie-Hellman protocol. The ECC Digital Signing
Combo Breaker, a DIY tool to easily crack many Master padlocks
May 16th, 2015 | 🕒
Powered by iSpeech The security expert Samy Kamkar after the disclosure of a method to easily crack many Master padlock
mSpy data breach exposes thousand kids to online predators
May 16th, 2015 | 🕒
Powered by iSpeech Recently e-mails, text messages, payments, locations, and other data related with mSpy users were posted on the
Chinese hackers used malware on Microsoft TechNet website to target other websites
May 16th, 2015 | 🕒
iSpeech.org Chinese hacking group APT17 and DeputyDog have been using Microsoft website TechNet for mounting attacks on other targets FireEye researchers
Fing – Find out Which Devices are Connected to your Wi-Fi Network
May 16th, 2015 | 🕒
https://www.ispeech.org/text.to.speech Find out which devices are connected to your Wi-Fi network, in just a few seconds. Fast and accurate, Fing
Plecost – WordPress Fingerprinting Tool
May 16th, 2015 | 🕒
https://www.ispeech.orgPlecost is a WordPress fingerprinting tool, it can search and retrieve information about the plug-in versions installed in a WordPress
Installing Python in Kali Linux
May 16th, 2015 | 🕒
Text to Speech Voices In this video, we note that Kali Linux comes with Python installed by default, compare 2.x
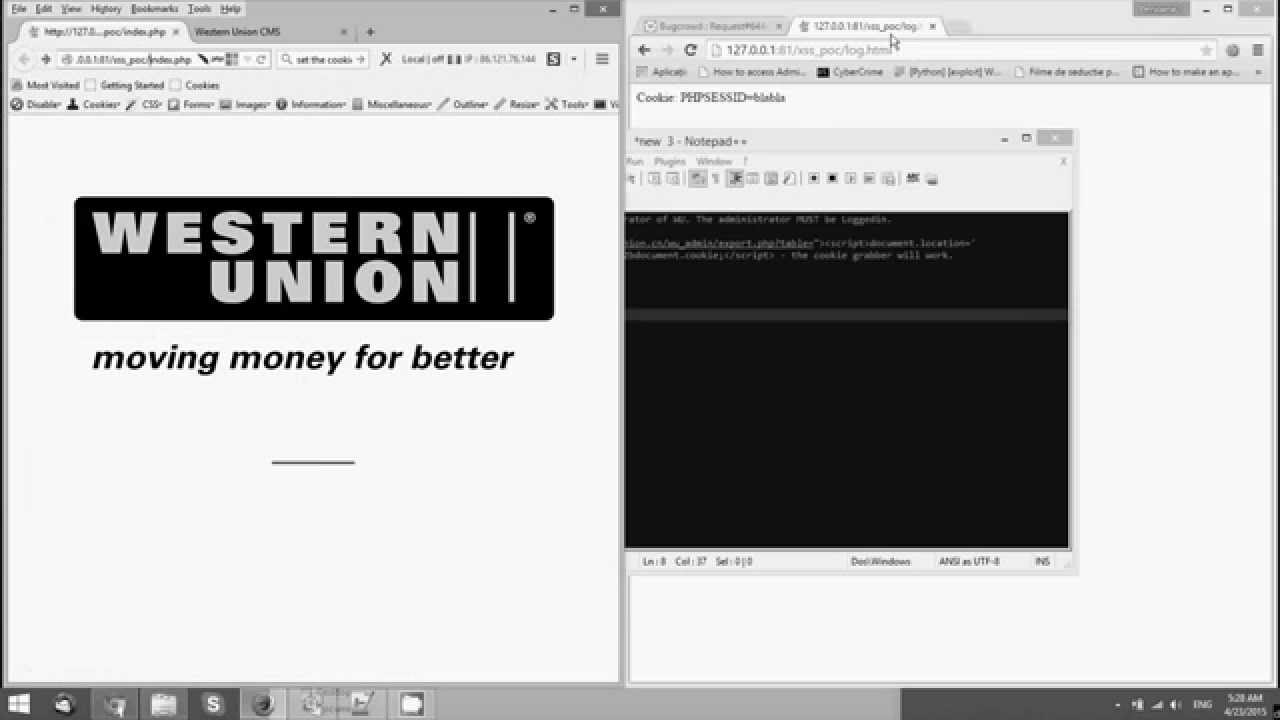
Cookie Stealer – PoC – Western Union China (Bug Bounty Program)
May 16th, 2015 | 🕒
Text to Voice 2015-05-16 05:14:51 source
Cross-Site Scripting – Western Union China (Bug Bounty Program)
May 16th, 2015 | 🕒
Text to Voice 2015-05-16 04:58:47 source
¿Cómo hacer un pentest o penetration testing?
May 16th, 2015 | 🕒
iSpeech http://www.dragonjar.org/pentesting/ ¿Cómo hacer un pentest o penetration testing? esta es solo el primer modulo del curso GRATUITO e introductorio


















Gloss