February 16th, 2014 | 🕒
iSpeech.org http://profitabletradingtips.com/stock-trading/trading-target-stock-after-the-data-breach Trading Target Stock after the Data Breach By www.ProfitableTradingTips.com As many as 110 million credit and debit cards
February 16th, 2014 | 🕒
https://www.ispeech.orgOWASP Xenotix XSS Exploit Framework is an advanced Cross Site Scripting (XSS) vulnerability detection and exploitation framework. It provides Zero
February 16th, 2014 | 🕒
iSpeechGoLismero is an open source framework for security testing. It’s currently geared towards web security, but it can easily be
February 16th, 2014 | 🕒
TTSDamn Vulnerable iOS App (DVIA) is an iOS application that is damn vulnerable. Its main goal is to provide a
February 16th, 2014 | 🕒
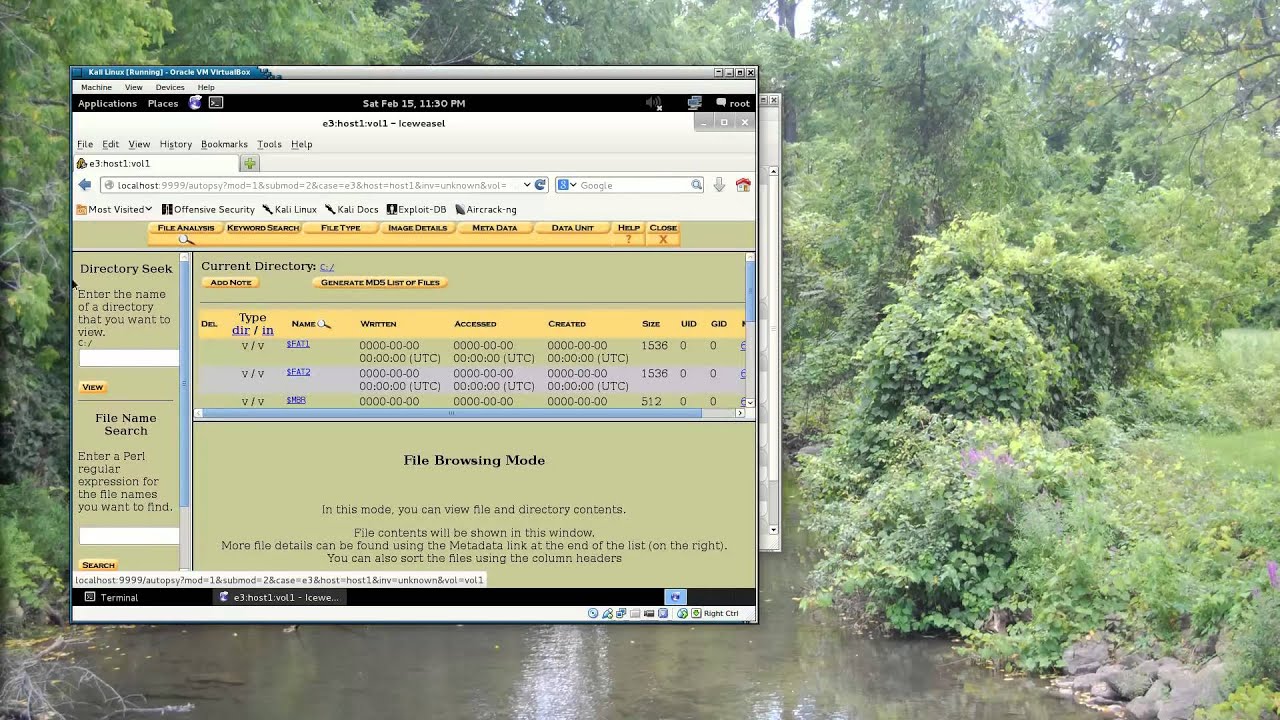
iSpeech Using the Autopsy forensic browser inside Kali Linux to explore the contents of a drive image 2014-02-16 00:00:16 source
February 16th, 2014 | 🕒
https://www.ispeech.org/text.to.speech Version with better audio at http://www.youtube.com/watch?v=JqJ4zaDIVAs A short tutorial on how to configure and use cree.py v1.1 Download cree.py











Gloss