February 5th, 2013 | 🕒
iSpeech Beat aus der "Rusty Loops EP" --- Download: http://www.mediafire.com/?n3cml2bc7k3wci0 FacebookKotze: https://www.facebook.com/pages/Defcon-Storch-Hader-EDS-Leipzig-Beats-Raps/113995012026607 video, sharing, camera phone, video phone, free, upload
February 5th, 2013 | 🕒
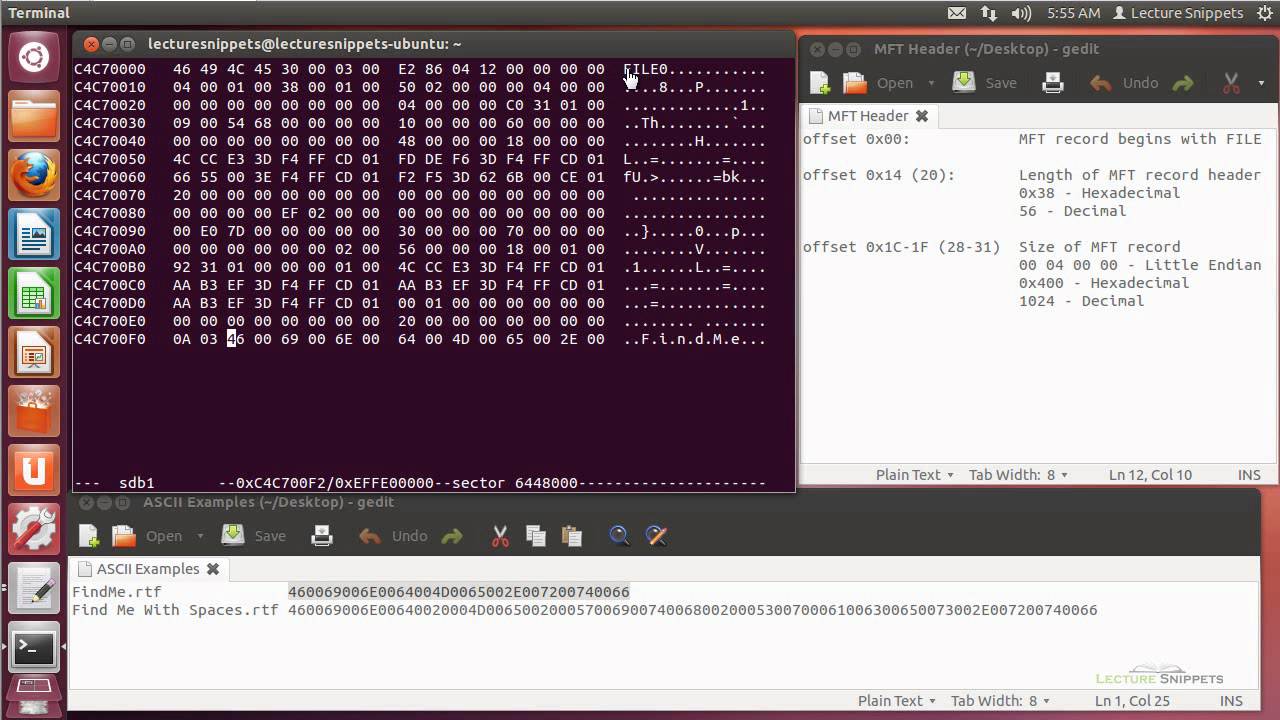
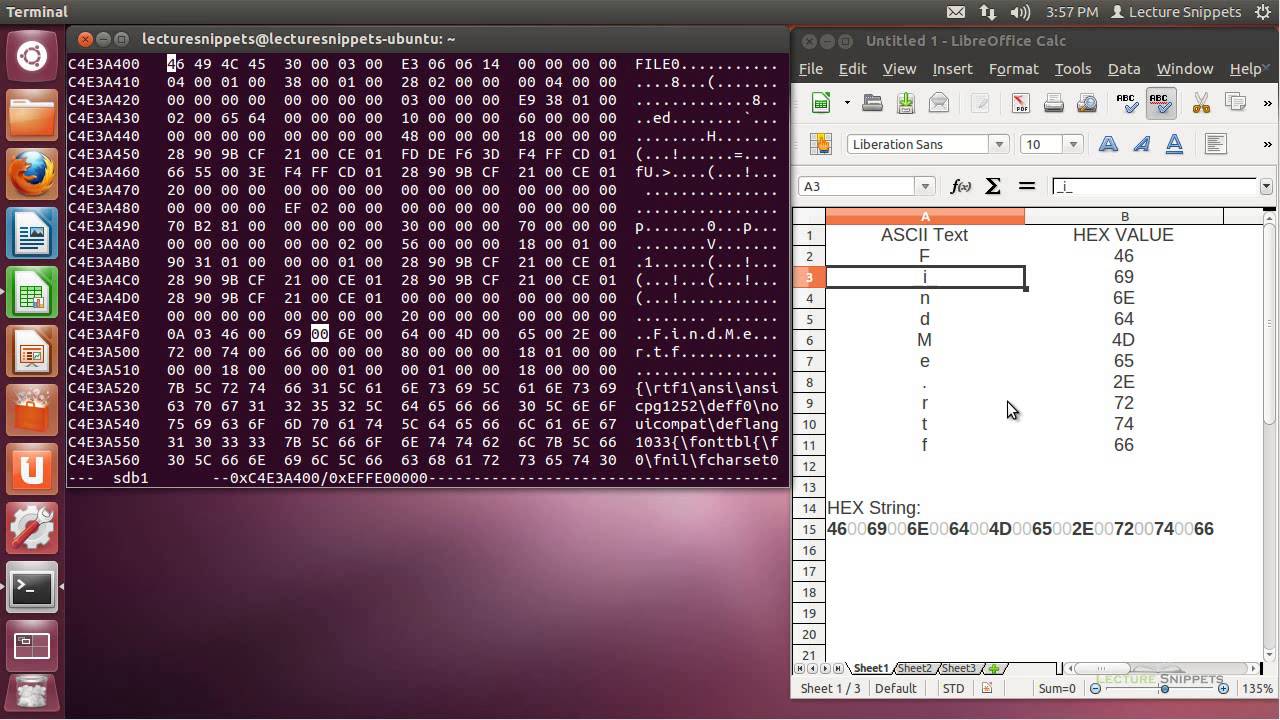
Text to Speech Demo File Downloads at http://lecturesnippets.com/downloads/ This video is part of a series on Computer Forensics using Ubuntu
February 5th, 2013 | 🕒
https://www.ispeech.org/text.to.speech File Downloads at http://lecturesnippets.com/downloads/ This video is part of a series on Computer Forensics using Ubuntu 12.04. In this
February 5th, 2013 | 🕒
iSpeech.org This video is part of a series on Computer Forensics using Ubuntu 12.04. In this Lecture Snippet I convert
February 4th, 2013 | 🕒
Powered by iSpeech The Times's David E. Sanger discusses a secret legal review concerning President Obama's powers in the face
February 4th, 2013 | 🕒
Text to Speech Magic attack animation done using Flash CS 5.5. I did animations and fx. Character was draw by
February 4th, 2013 | 🕒
iSpeech.org The medium of video is used to highlight observations and address areas of vulnerabilty in regard to the onset
February 4th, 2013 | 🕒
dutch tts Demonstration of web application security hacking, sql injection. sqlmap, fuzzDB, data encoding and data filtering, statement parameterization. 2013-02-03
February 1st, 2013 | 🕒
Text to Voice In the voices of researchers, public officials, and villagers, this documentary highlights a selection of problems and
February 1st, 2013 | 🕒
tts Sorry for the break in videos, here's number 3! It's all about unions, and I don't just mean my
February 1st, 2013 | 🕒
Powered by iSpeech TimesCast: Chinese hackers infiltrated The New York Times's computer systems, getting passwords for its reporters and others.
















Gloss