July 16th, 2011 | 🕒
https://www.ispeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 5: Hash Functions++ Sections 5.9.3 information hiding, steganography
July 16th, 2011 | 🕒
iSpeech.org Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 5: Hash Functions++ Section 5.9.2 random numbers Class
July 16th, 2011 | 🕒
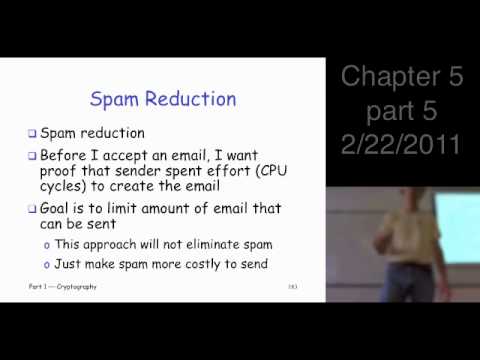
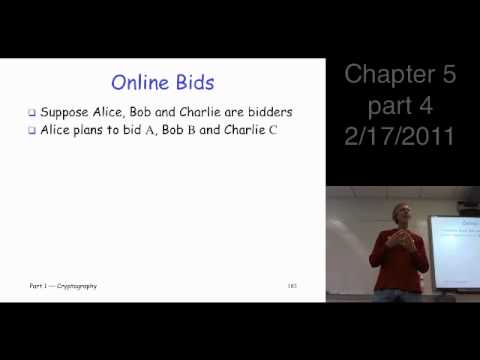
iSpeech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 5: Hash Functions++ Section 5.8.2 hash functions, uses
July 16th, 2011 | 🕒
https://www.ispeech.org/text.to.speech Information Security: Principles and Practice, 2nd edition, by Mark Stamp Chapter 5: Hash Functions++ Sections 5.8-5.8.1 hash functions, uses
July 16th, 2011 | 🕒
https://www.ispeech.org/text.to.speech










Gloss